Why are UAE enterprises spending an average of 450,000 د.إ annually on log storage when a 2024 study showed 58% of local security leads still face visibility gaps across their remote environments? You’ve likely felt the pressure of managing an overwhelming influx of alerts that don’t always translate into actionable defense. It’s exhausting to balance the high costs of data ingestion with the urgent need for real-time protection. Understanding the nuances of siem vs edr isn’t just a technical checkbox; it’s a strategic decision that defines your operational resilience in a market where threats evolve faster than budgets. You deserve a security architecture that works for your specific business goals rather than against your bottom line.
In this guide, you’ll master the critical differences between these two powerhouses to architect a resilient, future-proof security operations center. We’ll provide a clear roadmap for prioritizing your investments and show you how to integrate these tools into a unified SOC. You’ll learn how to reduce your mean time to detect by 40% while ensuring your strategy aligns with UAE NESA standards. We’re moving beyond the hype to deliver a bespoke approach that balances human intelligence with machine precision.
Key Takeaways
- Understand the fundamental architectural roles of SIEM as your network’s centralized intelligence and EDR as the granular, device-level defense mechanism.
- Navigate the technical nuances of siem vs edr by comparing telemetry sources and data retention strategies to ensure your SOC meets both forensic and compliance needs.
- Learn to prioritize security investments based on whether your organization requires a “Compliance First” approach for UAE GRC standards or a “Response First” posture against active ransomware.
- Discover how to bridge operational silos through bespoke integration, creating a unified ecosystem where SIEM and EDR work in a continuous feedback loop.
- Architect a future-proof security roadmap that aligns high-level digital transformation with the localized regulatory landscape of the National Enterprise.
Bridging the Visibility Gap: Why the SIEM vs. EDR Debate Matters in 2026
Security leaders in the UAE no longer view cybersecurity as a perimeter problem. As we move through 2026, the architecture of defense has shifted toward two critical pillars: Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR). We define SIEM as the centralized brain of your security operations. It functions by aggregating and correlating logs from every corner of your network, including firewalls, cloud instances, and applications. Conversely, EDR represents the boots on the ground. It provides microscopic visibility and automated response capabilities directly at the device level, whether it’s a workstation in Dubai Internet City or a server in an Abu Dhabi data center.
The urgency of the siem vs edr discussion is driven by a radical escalation in threat sophistication. In 2025, AI-driven phishing and deepfake identity fraud increased by 45% across the GCC. These attacks bypass traditional firewalls with ease. Furthermore, the UAE Cyber Security Council and the Dubai Electronic Security Center (DESC) have tightened mandates. Enterprises failing to maintain comprehensive monitoring now face regulatory scrutiny and potential fines that can exceed 500,000 AED under updated data protection frameworks. Relying on a single layer of defense is no longer a viable business strategy.
The Evolution of Detection and Response
Traditional antivirus solutions became obsolete when fileless malware and living-off-the-land attacks began to dominate the landscape. This failure triggered the EDR revolution, moving security from static signature matching to dynamic behavioral analysis. Simultaneously, SIEM evolved from a passive log storage vault into an advanced platform powered by User and Entity Behavior Analytics (UEBA). At OAD Technologies, we’ve seen that managing these hybrid-cloud environments requires an Expert Architect approach. It’s not just about owning the tools; it’s about engineering a system where data flows seamlessly between disparate cloud providers and on-premise infrastructure.
The Core Objective: Visibility vs. Actionability
The fundamental difference lies in the lens through which you view your data. SIEM offers a bird’s-eye view, identifying patterns across the entire enterprise to spot lateral movement. EDR provides a microscopic focus, allowing you to isolate a single infected laptop before a breach spreads. The Visibility Gap is the primary vulnerability for modern enterprises where blind spots between siloed data streams allow threats to persist undetected. By resolving this gap, we help organizations achieve Digital Resilience. This isn’t just about stopping an attack; it’s about ensuring your business operations remain uninterrupted and your long-term digital relevance is protected against an unpredictable 2026 threat landscape.
When evaluating siem vs edr, consider these operational realities:
- SIEM: Best for compliance, cross-platform correlation, and long-term forensic history.
- EDR: Essential for rapid containment, process-level monitoring, and neutralizing threats at the source.
Decoding the Mechanics: A Technical Comparison of SIEM and EDR
Choosing between SIEM and EDR requires a clear understanding of their technical DNA. SIEM acts as a centralized brain, ingesting logs from firewalls, servers, and cloud applications to provide a broad view of the infrastructure. In contrast, EDR functions as a specialist, capturing kernel-level telemetry directly from endpoints like laptops and servers. This distinction in data sources defines their utility; SIEM identifies lateral movement across the network, while EDR spots malicious code execution on a specific machine.
The response capabilities of these tools highlight their operational differences. EDR provides immediate, surgical actions, such as isolating a compromised host or killing a specific process. SIEM doesn’t typically interact with hardware directly. Instead, it triggers external workflows through SOAR platforms or ticketing systems. Integrating AI and Machine Learning has transformed both. By 2025, AI-driven triage reduced false positive alerts by 42% in UAE security operations centers, allowing teams to focus on high-priority threats rather than manual log review. This automation is essential for maintaining a lean, effective security posture.
Data Ingestion and Storage Architecture
SIEM follows a “Log Everything” philosophy to meet compliance mandates like the UAE NESA standards. This requires massive storage capacity for long-term retention. EDR is “Event-Driven,” focusing on high-fidelity, short-term data for rapid forensics. In 2026, security budgets in Dubai must account for rising cloud storage costs, where high-performance indexing can reach 65,000 AED per terabyte annually. Achieving a balance requires SIEM integration that prioritizes actionable data over raw volume. OAD Technologies helps firms architect these systems to maximize visibility without overextending budgets.
Detection Logic and Threat Hunting
The siem vs edr debate often centers on detection methodology. SIEM uses correlation rules to link disparate events, such as a failed login on a VPN followed by a database export. EDR employs behavioral analysis to detect “living-off-the-land” techniques, where attackers use legitimate system tools for malicious ends. Both platforms now map their coverage to the MITRE ATT&CK framework, ensuring that 90% of known adversary tactics are visible to the security team. This structured approach allows for proactive threat hunting rather than reactive firefighting. If you’re looking to refine your stack, you can consult our technical architects to design a bespoke detection strategy.
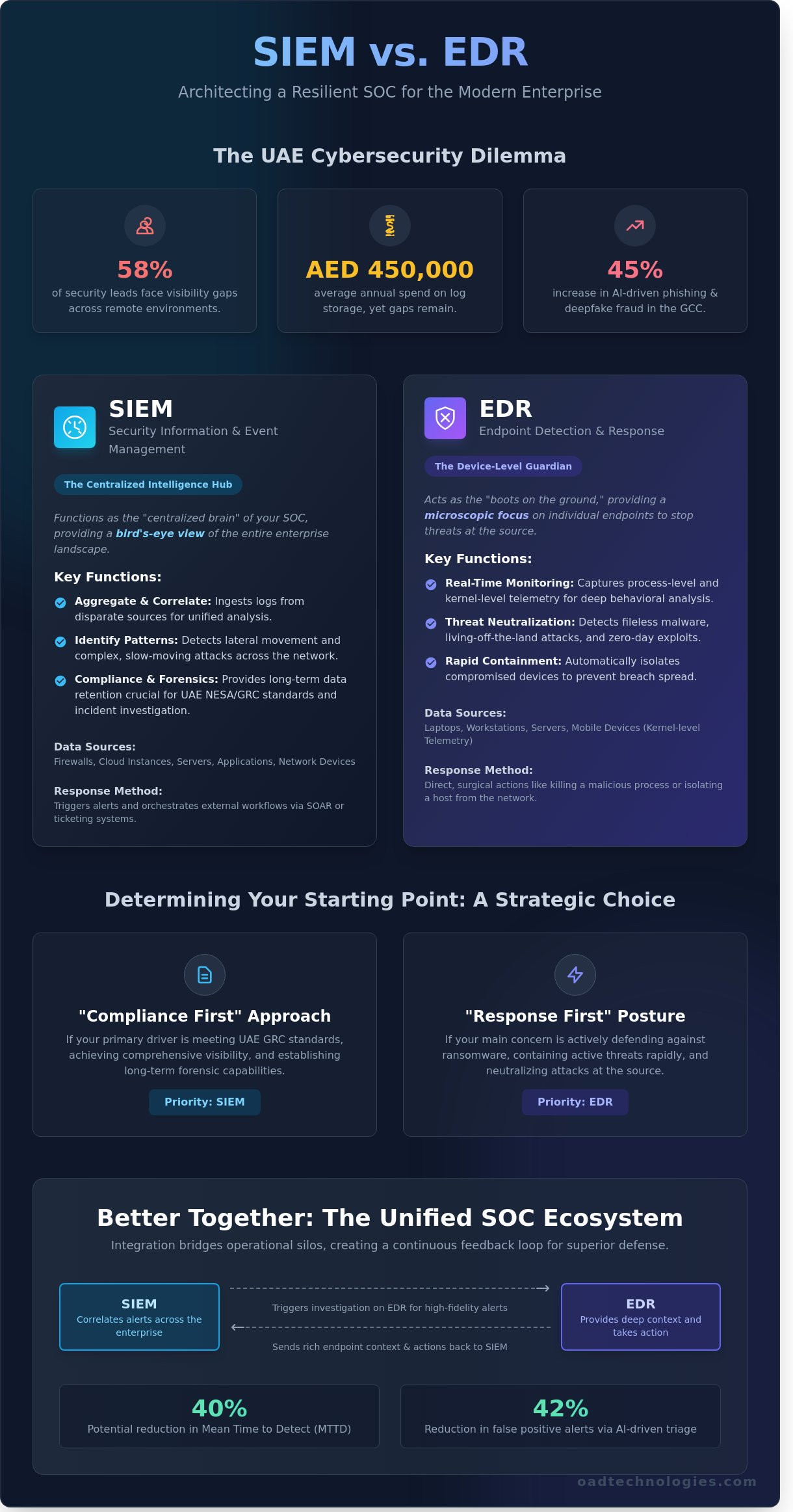
The Strategic Dilemma: Evaluating SIEM vs. EDR for Your Security Maturity
Deciding between siem vs edr isn’t a matter of which tool is superior; it’s a question of which risk profile you need to mitigate today. In the UAE, 68% of organizations reported a surge in sophisticated ransomware attempts throughout 2023. This reality forces a strategic choice: do you prioritize the broad visibility required for compliance, or the surgical response needed to kill a live threat? Your current security maturity level dictates the answer.
The total cost of ownership (TCO) remains a deciding factor for many CFOs in the region. A robust SIEM implementation often demands an initial investment exceeding 150,000 AED for licensing, plus the recurring cost of a specialized team. Since the average salary for a SOC lead in Dubai hovers around 35,000 AED per month, the human capital requirement is steep. EDR scales differently, typically priced between 180 AED and 450 AED per endpoint annually. It’s often more accessible for rapid deployment across a distributed workforce, though it lacks the holistic view of the network.
A frequent error among IT directors is the belief that EDR’s advanced detection capabilities make a SIEM redundant. This isn’t the case. EDR acts as a high-powered microscope for your workstations; SIEM is the command center’s radar for your entire digital estate. Relying solely on one creates dangerous blind spots in your security posture that attackers will eventually exploit.
When to Prioritize SIEM Implementation
Organizations should lead with SIEM when compliance with NESA (National Electronic Security Authority) or SIA standards is mandatory. These frameworks often require 180 days or more of log retention for forensic auditing. SIEM is also the only way to monitor non-endpoint assets, such as IoT sensors in smart buildings or legacy industrial control systems (ICS) that won’t support modern EDR agents.
When to Prioritize EDR Implementation
EDR takes precedence when your primary threat is ransomware targeting a remote workforce. Since 42% of UAE employees now utilize hybrid work models, the traditional network perimeter has dissolved. EDR ransomware protection provides immediate, automated containment. It allows you to isolate a compromised laptop in Sharjah before the infection reaches your main data center in Abu Dhabi, providing the granular forensics needed to understand the breach’s root cause.
Beyond the Silos: Architecting a Unified Detection and Response Ecosystem
Smart security leaders don’t view the siem vs edr choice as a binary decision. They treat it as an architectural challenge. Bespoke integration means tailoring your security stack to your specific UAE infrastructure, whether you’re managing a hybrid cloud environment in Dubai or a strictly on-premise government facility in Abu Dhabi. When these tools work in isolation, they create blind spots. When they’re integrated, they form a feedback loop that significantly hardens your posture. SIEM provides the historical depth and broad visibility, while EDR offers the granular control needed to stop a threat in its tracks.
This integration is the foundation of Extended Detection and Response (XDR). XDR isn’t just a buzzword; it’s the natural evolution of merging endpoint, network, and cloud telemetry. To bridge the operational gap between these tools, Security Orchestration, Automation, and Response (SOAR) plays a critical role. By automating 35% of routine investigative tasks, SOAR allows your team to focus on high-priority threats. It ensures that an alert in your EDR can automatically trigger a wider search across your SIEM logs to see if other assets are compromised.
The Power of Integrated Telemetry
EDR data enriches SIEM alerts by providing the “how” behind an incident. If your SIEM flags a login from an unusual IP, your EDR can immediately confirm if that specific endpoint executed a PowerShell script at the same time. This context reduces false positives by roughly 42%, saving hours of wasted investigation. A unified dashboard gives your SOC team a single source of truth, improving operational efficiency and reducing the Mean Time to Respond (MTTR) by up to 60% compared to siloed workflows.
The Path to MDR: Managed Detection and Response
Software licenses alone won’t protect your data. Even the most sophisticated siem vs edr setup requires 24/7 human oversight to interpret complex attack patterns. In the UAE, where 65% of organizations report difficulty finding specialized cybersecurity talent, the managed service model is often the most cost-effective route. Our MDR guide details how this model provides the Expert Architect role your business needs to maintain a resilient ecosystem. We ensure your technology empowers your people, rather than overwhelming them with noise.
Ready to move beyond basic toolsets? Partner with our security architects to build your bespoke defense.
Future-Proofing with OAD Technologies: Strategic Security for the National Enterprise
OAD Technologies serves as the Expert Architect for organizations across the United Arab Emirates. We don’t just implement software; we engineer resilience by bridging the gap between high-level innovation and tangible business results. Our team understands that the siem vs edr debate isn’t just about technical specifications. It’s about how these tools integrate into your specific operational workflow while meeting local GRC requirements like the UAE National Cyber Security Strategy and SIA (formerly NESA) standards.
Deploying security tools without validation creates a false sense of safety. We utilize rigorous Vulnerability Assessment and Penetration Testing (VAPT) to stress-test your infrastructure. If your SIEM fails to trigger an alert within 120 seconds of a simulated lateral movement, our engineers re-calibrate your correlation rules. This proactive architecture ensures your digital relevance remains intact as your enterprise scales toward 2026.
Bespoke Security Solutions
We reject the one-size-fits-all model that dominates the market. OAD designs infrastructure-specific protection that accounts for the unique data flows of your business. By integrating Data Loss Prevention (DLP) with your existing monitoring tools, we create a unified defense layer. Our engineering standards ensure that a 20% increase in log volume doesn’t lead to alert fatigue or system latency. We focus on long-term client success by building systems that empower your team rather than complicating their daily tasks.
Next Steps: Securing Your 2026 Roadmap
A 2023 study by IDC indicated that 72% of UAE organizations are increasing their security spending to meet evolving regulatory demands. Your 2026 roadmap requires a strategic assessment of your current stack to ensure every AED invested delivers maximum protection. The siem vs edr priority should be determined by your specific risk profile and current maturity level.
- Evaluate: Conduct a gap analysis of your existing detection capabilities.
- Architect: Consult with OAD’s Expert Architects to design a tailored deployment plan.
- Optimize: Focus on operational efficiency to drive strategic growth.
Don’t leave your enterprise’s safety to chance or generic configurations. Reach out to OAD Technologies today to schedule a technical consultation. We’ll help you move beyond reactive patching and toward a future of architected, proactive security.
Architecting Your Resilient UAE Security Posture
The choice between siem vs edr isn’t a binary decision; it’s a strategic architectural evolution. By 2026, UAE enterprises must move beyond siloed visibility to achieve a unified detection posture. Effective security requires the deep endpoint forensics of EDR coupled with the broad log correlation of SIEM to eliminate blind spots across cloud and on-premise environments.
OAD Technologies acts as your Expert Architect in this journey. We provide UAE-based SOC expertise and 24/7 monitoring as a premier Managed Security Services Provider. Our security architectures undergo rigorous VAPT validation to ensure your defenses remain impenetrable against evolving regional threats. We don’t believe in generic templates. We build bespoke ecosystems that align your technical maturity with long-term business growth.
Consult with an OAD Expert Architect to design your bespoke SIEM and EDR strategy and secure your organization’s digital relevance today. Your path to a resilient, future-proof enterprise starts with a single strategic alignment.
Frequently Asked Questions
Can EDR replace a SIEM in a modern SOC?
EDR cannot replace a SIEM because it lacks visibility into network hardware, cloud control planes, and legacy applications. While EDR provides deep endpoint telemetry, a SIEM aggregates data across your entire UAE enterprise architecture. Most local SOCs find that EDR only covers 45% of the total attack surface. You need the SIEM to correlate those endpoint events with firewall logs and identity provider data for a complete security picture.
How do SIEM and EDR work together to stop ransomware?
SIEM and EDR create a multi-layered defense where the EDR kills malicious processes on the device while the SIEM identifies broader patterns of lateral movement. In a 2023 analysis of ransomware attacks in the Middle East, integrated systems reduced dwell time by 50%. The EDR acts as the local enforcement officer. The SIEM serves as the central command center, ensuring a single compromised workstation doesn’t lead to a full network lockout.
What is the cost difference between managing SIEM in-house vs. an MDR service?
Managing an in-house SIEM in the UAE typically costs upwards of 650,000 د.إ per year when you factor in licensing and a 24/7 team of four analysts. An MDR service often reduces these operational expenses by 40% through shared infrastructure and automated playbooks. This shift allows your internal team to focus on strategic digital transformation rather than triaging thousands of low-level alerts daily. It’s a more scalable model for growing firms.
Do I need a SIEM for compliance if I already have EDR logs?
You generally need a SIEM to meet UAE NESA or Dubai Information Security Regulation (ISR) requirements for centralized log retention and correlation. EDR logs are valuable, but they don’t fulfill the 12 month retention mandates for non-endpoint sources like VPNs and database servers. Implementing a siem vs edr strategy ensures you capture the 100% of audit logs required by local regulators to pass annual compliance audits.
How does XDR differ from integrating SIEM and EDR manually?
XDR provides a pre-integrated ecosystem that eliminates the manual API configuration required to link a standalone siem vs edr setup. Traditional manual integration can take 3 to 5 months of engineering time to normalize data fields correctly. XDR unifies these streams out of the box. It offers a more seamless experience for security teams who want immediate visibility without the heavy lifting of custom coding or complex data mapping.
What are the most common integration challenges between SIEM and EDR?
High data ingestion costs and alert fatigue from non-normalized data are the primary hurdles during integration. Many UAE firms see their SIEM costs spike by 30% when they first ingest raw EDR telemetry without proper filtering. You must map EDR attributes to a Common Information Model (CIM) to ensure your correlation rules trigger accurately. Without this precision, your analysts will waste 4 hours a day chasing duplicate alerts that lack context.
Is EDR effective for protecting cloud-native environments?
EDR is only partially effective for cloud-native environments because it can’t monitor serverless functions or cloud management consoles. It’s designed for the OS level, but modern UAE businesses increasingly rely on SaaS and PaaS layers. You’ll need to augment EDR with Cloud Workload Protection Platforms (CWPP) or a SIEM that ingests logs from Azure or AWS. This ensures you catch unauthorized configuration changes that an endpoint agent simply won’t see.
How often should SIEM correlation rules be updated to stay effective?
You should update your SIEM correlation rules at least once every 30 days to account for evolving threat actor tactics. The MITRE ATT&CK framework adds dozens of new techniques annually, requiring your logic to stay current. If you haven’t tuned your rules in the last 90 days, your detection efficacy likely dropped by 20%. Regular audits ensure your security posture remains resilient against the 2024 threat landscape in the Middle East.


