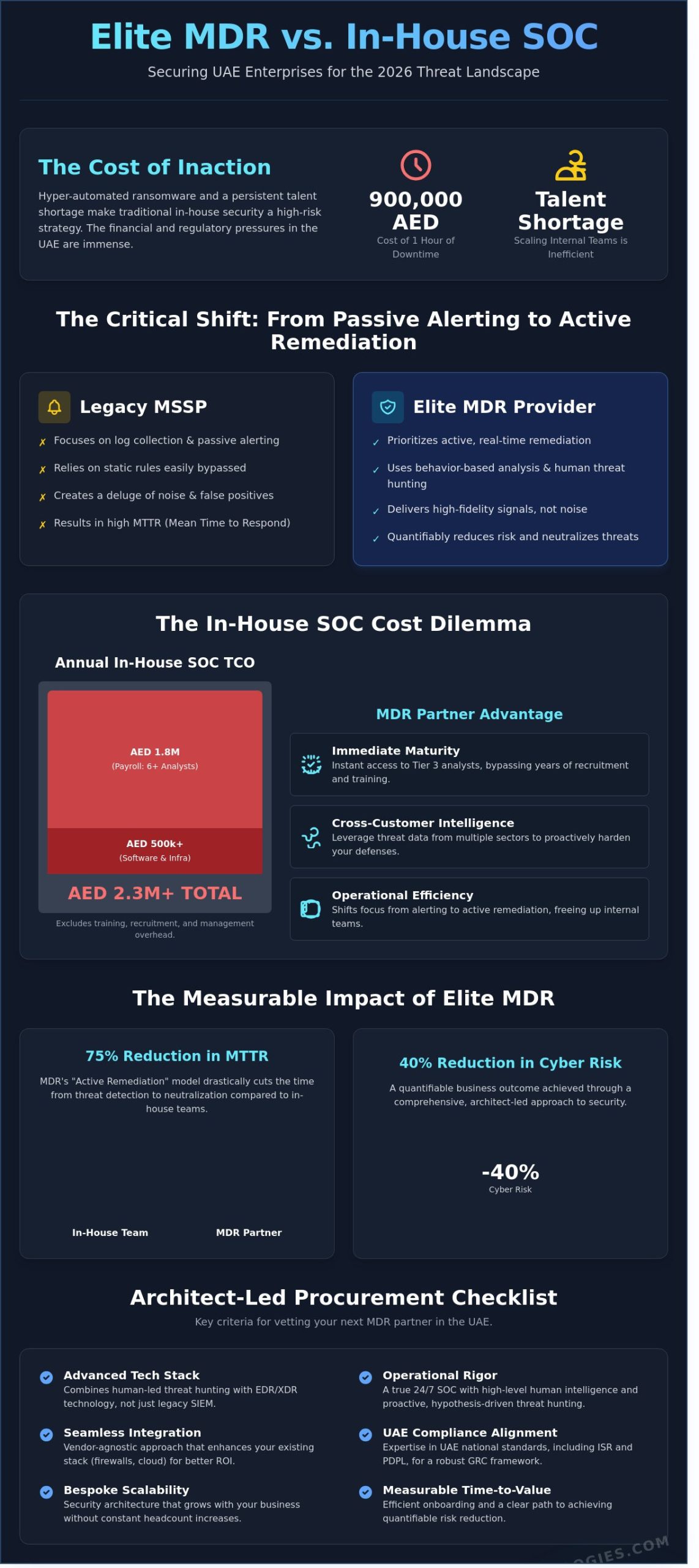
The traditional approach to in-house security is no longer a viable defense strategy for UAE enterprises facing 2026’s hyper-automated ransomware variants. You’ve likely realized that the persistent cybersecurity talent shortage in the region makes scaling an internal team both costly and inefficient. When a single hour of downtime can cost a Dubai-based enterprise upwards of 900,000 AED, the pressure to maintain 24/7 vigilance while meeting strict ISR and PDPL compliance standards is immense. Selecting the right mdr provider is the most critical architectural decision your leadership will make this year to secure your digital transformation.
We’ve built this guide to move beyond generic service level agreements and focus on tangible business outcomes. You’ll gain access to a comprehensive, architect-led procurement checklist designed to ensure your chosen partner delivers a quantifiable 40% reduction in cyber risk. We’ll explore how to achieve seamless integration with your existing stack, providing the peace of mind that comes from a bespoke security posture tailored for the UAE’s unique regulatory environment.
Key Takeaways
- Distinguish between legacy MSSPs and elite services that combine human-led threat hunting with advanced EDR/XDR technology to counter the 2026 threat landscape.
- Audit a provider’s technical stack for seamless SIEM integration and bespoke scalability to ensure your security architecture remains future-proof.
- Evaluate the operational rigor of a 24/7 SOC to guarantee that your defense model leverages high-level human intelligence alongside automated detection.
- Ensure strategic alignment with UAE national standards, including ISR and PDPL, to effectively integrate your security posture within a robust GRC framework.
- Utilize a 10-point architect-led checklist to vet your next mdr provider based on onboarding efficiency and measurable Time to Value.
Defining the Core Capabilities of an Elite MDR Provider
Managed Detection and Response (MDR) has evolved beyond simple outsourced monitoring. It’s now a sophisticated fusion of Extended Detection and Response (XDR) technology and continuous human-led threat hunting. By 2026, the distinction between a standard mdr provider and a traditional Managed Security Service Provider (MSSP) is absolute. While MSSPs focus on log collection and passive alerting, an elite MDR service prioritizes active remediation. This shift ensures that threats are neutralized in real-time, preventing the lateral movement that leads to catastrophic data loss.
OAD Technologies approaches security as an Expert Architect. We don’t just deploy tools; we design bespoke security frameworks that integrate seamlessly with your existing infrastructure. This methodology moves away from the “black box” service model toward a collaborative partnership. We focus on high-fidelity signals rather than a deluge of noise, ensuring your internal teams stay focused on strategic growth rather than chasing false positives.
The Evolution of Managed Detection and Response
Legacy SIEM monitoring relied on static rules that attackers easily bypassed. Modern MDR utilizes behavior-based analysis to detect anomalies that signature-based tools miss. In the 2026 threat environment, AI handles 90% of initial alert triage. This allows human analysts to focus on complex investigations. Full-stack visibility is mandatory. Your mdr provider must monitor cloud environments, network traffic, and every endpoint to comply with the UAE’s Federal Decree-Law No. 45 of 2021 regarding personal data protection.
Why Managed Services Outperform In-House SOCs
The total cost of ownership (TCO) for a 24/7 in-house Security Operations Center (SOC) in the UAE is often prohibitive. A minimum viable team requires at least six analysts to cover three shifts. With average salaries for cybersecurity professionals in Dubai currently around AED 25,000 per month, annual payroll alone exceeds AED 1.8 million. This doesn’t include the AED 500,000 or more required for software licenses and infrastructure.
- Immediate Maturity: MDR provides instant access to Tier 3 analysts that would take years to recruit and train.
- Cross-Customer Intelligence: Threats detected in the UAE financial sector are immediately used to harden defenses for retail and healthcare clients.
- Scalability: Your security posture grows with your business without the need for constant headcount increases.
- Operational Efficiency: Shifting from an “Alerting” model to “Active Remediation” reduces the mean time to respond (MTTR) by 75% compared to in-house teams.
Partnering with a provider ensures you benefit from a collective defense strategy. This approach offers a level of resilience that isolated in-house teams simply cannot match. It bridges the gap between high-level innovation and practical business results while future-proofing your digital assets.
Technical Evaluation: Detection, Response, and Remediation
Selecting an mdr provider requires a rigorous audit of their architectural choices. You must determine if they utilize a proprietary “black box” or a vendor-agnostic stack that integrates with your current security investments. In the UAE market, where organizations often spend upwards of AED 200,000 on perimeter defenses, a provider’s ability to ingest data from existing firewalls and cloud instances is vital for ROI. A bespoke integration strategy ensures that your security posture remains cohesive rather than fragmented across disparate tools.
The Role of EDR and XDR in Modern MDR
EDR acts as the primary telemetry source, providing the deep forensic data needed to reconstruct attack paths. Most sophisticated threats now bypass traditional signatures, making endpoint visibility non-negotiable. We’re seeing a decisive shift toward XDR, which pulls data from identity, network, and cloud layers to provide a unified view. This holistic approach reduces the “silo effect” that contributed to a 15% increase in dwell times for Middle Eastern enterprises in 2024. Your partner should enhance, not replace, the tools you’ve already deployed.
Proactive Threat Hunting vs. Reactive Alerting
Effective defense isn’t just about waiting for a red light to flash. Proactive threat hunting is a hypothesis-driven search for hidden adversaries who’ve already bypassed your initial defenses. It involves manual investigation by senior analysts rather than simple automated scans. You should ask your potential partner how frequently they conduct these deep-dive hunts. Adversary Tracking is a core component of elite MDR, focusing on the specific behaviors of threat groups known to target UAE infrastructure and financial hubs.
Automated vs. Human-Led Remediation
Speed is critical, but unguided automation can disrupt business operations. SOAR platforms excel at high-speed, low-risk tasks like blocking malicious IPs or revoking compromised tokens. However, high-impact actions like isolating a production server require human expertise to prevent accidental downtime. You need to establish clear “Rules of Engagement” that define exactly what the provider can do autonomously. A tailored security roadmap helps balance these automated responses with human oversight to maintain operational continuity.
Performance must be measured through concrete metrics. Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) are the industry standards for accountability. Leading providers in 2025 are achieving an MTTR of under 30 minutes for critical incidents. If a provider’s “response” is merely an email notification, they’re failing to provide true remediation. Demand a partner that takes active steps to neutralize threats before they escalate into full-scale breaches.
Operational Excellence: 24/7 SOC and Expert Human Intelligence
Technology alone cannot secure a modern enterprise. The true value of a premium mdr provider lies in the caliber of the professionals operating the Security Operations Center (SOC). By 2026, the distinction between a “ticket-factory” and a strategic partner will be defined by the “Expert Architect” persona. This model moves beyond simple alert forwarding; it provides actionable engineering guidance that integrates with your specific infrastructure. When evaluating providers, prioritize a ratio of at least one senior analyst for every 200 daily critical alerts. This ensures that your environment receives focused attention rather than a cursory glance from an overworked technician.
Coverage must be absolute. For UAE-based firms, this often requires a “follow the sun” model that maintains 24/7/365 vigilance while adhering to local data residency regulations like the Dubai Electronic Security Center (DESC) standards. A dedicated national team offers the advantage of understanding the regional threat landscape, such as specific phishing campaigns targeting UAE financial institutions. You should demand a service level agreement (SLA) that guarantees a human response to critical threats within 15 minutes, regardless of whether the alert triggers at 2:00 PM or 2:00 AM GST.
Vetting the Human Intelligence Behind the Screen
Certifications serve as the baseline for technical proficiency. Look for teams holding GIAC Certified Incident Handler (GCIH), Offensive Security Certified Professional (OSCP), or GIAC Certified Forensic Analyst (GCFA) credentials. These designations prove the staff can handle complex post-exploitation scenarios. To combat “Analyst Fatigue,” which affected 72% of global SOC teams in 2024, ask how the provider rotates shifts and automates mundane tasks. High-performing providers invest in their staff’s mental clarity to ensure they don’t miss the one subtle indicator of a sophisticated breach.
Transparency and Reporting Standards
Static monthly PDFs are obsolete. Your mdr provider must offer a real-time dashboard that reflects the current state of your security posture. These platforms should translate technical telemetry into “Executive-Ready” insights, allowing a CISO to present the security ROI in AED to the board of directors. Effective reporting includes:
- Detailed forensic timelines of every mitigated incident.
- Root cause analysis to prevent repeat vulnerabilities.
- Strategic recommendations for hardware or software configuration changes.
- Clear metrics on Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR).
This level of transparency ensures the provider acts as a transparent extension of your internal team, not a black box.
Strategic Alignment: Compliance, GRC, and National Standards
Selecting an mdr provider isn’t just a technical decision. It’s a strategic move to ensure your organization remains on the right side of UAE law. As we approach 2026, the regulatory environment is becoming more rigorous, demanding that security operations align perfectly with national mandates. Your provider must act as a bridge between raw technical telemetry and your high-level Governance, Risk, and Compliance (GRC) objectives.
Meeting National Regulatory Requirements
The UAE Information Assurance (IA) standards and the 2021 Personal Data Protection Law (PDPL) set high bars for data handling and incident response. Your mdr provider must offer a local footprint to ensure data sovereignty. If your security telemetry or sensitive logs leave the UAE, you risk non-compliance with the UAE ISR. Fines for data mishandling under PDPL can reach 1,000,000 AED or more depending on the severity of the breach. OAD Technologies prioritizes local data residency to keep your operations legally sound and culturally aligned with regional expectations.
Integrating MDR with GRC and Risk Management
Modern security leaders use MDR data to inform their corporate risk register in real time. Instead of relying on static annual assessments, use the continuous monitoring data to validate your security controls for audit purposes. A 2024 industry report indicated that 87% of regional CISOs who integrated MDR feeds into their GRC platforms reduced their audit preparation time by 40%. This integration allows you to:
- Provide evidence of active threat hunting for regulatory bodies.
- Identify gaps in your Data Loss Prevention (DLP) strategies before they lead to a leak.
- Adjust your risk appetite based on actual threat actor behavior targeting the UAE financial or energy sectors.
A sophisticated partner also assists in technical assessments like VAPT. They don’t just alert you to a problem; they provide the technical context needed to remediate vulnerabilities discovered during penetration tests. This proactive approach ensures that your security posture evolves faster than the threats it faces.
The Final Procurement Checklist: Vetting Your MDR Partner
Selecting an mdr provider requires more than a standard software demo. It demands a rigorous examination of how a partner aligns with your operational reality. In the UAE, where cyber threats are increasingly sophisticated, a cookie-cutter approach creates vulnerabilities. You need a partner that functions as a strategic architect, not just a vendor. This final stage is about verifying that their technical capabilities translate into tangible business resilience.
10 Essential Questions for Your MDR Provider
Final interviews should probe the depth of an mdr provider‘s expertise and their ability to scale. Ask these 10 questions to separate the leaders from the laggards:
- How do you tailor response playbooks to our specific business logic and UAE regulatory requirements like NESA?
- What specific experience do your analysts have in neutralizing national-level threat actors active in the Middle East?
- How does your AI roadmap for 2026 prioritize predictive threat hunting over reactive alerting?
- What is the average “Time to Value” for an enterprise of our size?
- How do you integrate human intelligence with machine learning to reduce false positives by at least 40%?
- Can you demonstrate a bespoke dashboard that reflects our specific risk profile?
- What is your process for maintaining 99.9% uptime for monitoring during regional network disruptions?
- How do your analysts stay updated on the latest TTPs used by regional APT groups?
- What specific metrics do you provide to demonstrate ROI in AED?
- How will you ensure our internal team retains visibility and control during a critical breach?
Onboarding and Long-Term Partnership
The first 90 days are critical for establishing a defensive baseline. A standard onboarding often fails because it ignores the nuances of local infrastructure and legacy systems. OAD Technologies utilizes a structured 30/60/90-day framework to ensure seamless integration. The first 30 days focus on deep architectural mapping and data ingestion. By day 60, we’ve tuned our engines to your environment, often reducing noise and false alerts by up to 65%. By day 90, we deliver full operational maturity with custom playbooks that reflect your unique business logic.
We address “Service Drift” through quarterly strategic reviews. This prevents the “set and forget” mentality that leads to 15% annual increases in undetected threats for unmanaged systems. We treat your security as a living architecture. Our team performs continuous tuning to ensure your defenses evolve alongside your digital transformation. This proactive stance ensures your investment remains future-proofed against emerging threats in 2026 and beyond.
Take the final step in your security journey. Secure your enterprise with OAD Technologies’ bespoke MDR services for an architected, national-standard defense.
Securing Your 2026 Digital Roadmap
Selecting the right mdr provider isn’t just a procurement task; it’s a strategic investment in your organization’s long-term resilience. By 2026, the UAE digital economy’s contribution to non-oil GDP is expected to reach 20%, making high-tier cyber defense a non-negotiable pillar for business continuity. You’ve identified that elite protection requires a fusion of 24/7 technical detection and deep human intelligence. It also demands a partner who masters the local regulatory landscape, including NESA and Dubai ISR standards, to ensure your GRC framework remains airtight.
OAD Technologies delivers this via our UAE-based SOC and a bespoke security architecture tailored to your specific risk profile. We prioritize precision over generic templates. Our engineers integrate end-to-end GRC and VAPT protocols to bridge the gap between high-level strategy and ground-level technical remediation. We’re here to help you navigate the evolving 2026 threat landscape with direct accountability and technical authority.
Take the next step in future-proofing your infrastructure. Request a Strategic MDR Consultation with OAD Technologies today to build a defense that scales with your ambition. We look forward to securing your digital future.
Frequently Asked Questions
What is the difference between an MDR provider and an MSSP?
An MDR provider delivers proactive threat hunting and rapid incident response, while an MSSP primarily manages security infrastructure and perimeter defense. MSSPs focus on log collection and alert generation; however, they often lack the deep forensic capabilities required for active remediation. A bespoke MDR service integrates directly with your team to neutralize threats within minutes, ensuring your digital transformation remains secure and resilient.
How much does an MDR service typically cost in 2026?
Expect to invest between AED 180 and AED 450 per endpoint annually for comprehensive coverage in 2026. These costs fluctuate based on the volume of data ingestion and the complexity of your hybrid cloud environment. A strategic partnership allows your business to scale its security spend in alignment with operational growth, delivering a measurable ROI through reduced risk and optimized resource allocation.
Does an MDR provider replace my existing IT security team?
No, this service is designed to augment your existing staff rather than replace them. This partnership empowers your internal IT team to pivot away from 24/7 monitoring and focus on high-value strategic initiatives. By offloading the technical burden of threat detection, your architects can prioritize innovation while the provider maintains the integrity of your digital ecosystem.
Can an MDR provider help with UAE PDPL compliance?
Yes, a qualified mdr provider helps you navigate the complexities of the UAE Personal Data Protection Law. Federal Decree Law No. 45 of 2021 mandates strict data residency and breach notification protocols. A localized provider ensures your data remains within UAE borders and provides the forensic evidence needed to meet the 72-hour reporting requirement specified by the UAE Data Office.
What is the typical onboarding time for a managed detection service?
Typical onboarding for a managed detection service spans 21 to 45 days. This timeline includes a 10-day architectural assessment followed by the deployment of sensors across your network. We follow a structured roadmap to ensure seamless integration, validating every data source before the 24/7 monitoring phase begins to ensure no visibility gaps remain in your infrastructure.
How does an MDR provider handle false positives?
Providers manage false positives by applying behavioral analytics and human-led verification to every alert. This dual-layered approach reduces alert noise by 92%, filtering out benign activities that often distract internal teams. By delivering only high-fidelity, actionable intelligence, the provider ensures your response efforts are focused on genuine threats that pose a real risk to your strategic growth.
Is MDR suitable for small to medium-sized enterprises (SMEs)?
MDR is highly suitable for SMEs with 50 to 500 employees that require enterprise-grade protection. Building an in-house Security Operations Center costs upwards of AED 1.5 million annually; however, a managed service provides the same capability for a fraction of that investment. It’s a scalable solution that allows smaller entities to maintain a robust security posture without heavy capital expenditure.
What happens if a breach occurs while using an MDR provider?
The provider initiates immediate containment protocols within 15 minutes of detecting a confirmed incident. They isolate compromised assets to stop lateral movement and begin a forensic investigation to identify the root cause. This rapid intervention minimizes downtime and protects your long-term digital relevance by preventing the significant financial and reputational damage often associated with prolonged data breaches.


