By 2026, industry data suggests that 95% of cloud security failures will stem from avoidable misconfigurations rather than sophisticated external attacks. You’re likely already feeling the strain of this reality as your multi-cloud environment expands. It’s exhausting to reconcile conflicting security protocols while your team battles compliance fatigue from manual reporting. This is why a robust strategy for cloud security posture management is no longer optional; it’s the foundation of your long-term digital relevance and strategic growth.
We’ve designed this guide to help you master a sophisticated framework that secures your digital assets against the specific threats of 2026. You’ll learn how to implement automated remediation and establish a unified security dashboard that provides total visibility across every asset you own. We’ll break down the transition from fragmented oversight to a bespoke, zero-leak environment that drives operational efficiency instead of hindering it. It’s time to move beyond quick fixes and architect a future-proof defense that empowers your team to scale with confidence.
Key Takeaways
- Identify the critical “invisibility gaps” created by rapid digital transformation and learn how to maintain total visibility across complex multi-cloud environments.
- Master the strategic application of cloud security posture management to automate the detection and remediation of misconfigurations before they become active vulnerabilities.
- Distinguish the unique roles within the cloud security trinity—CSPM, CWPP, and CASB—to ensure comprehensive protection that native provider tools often overlook.
- Transition from rigid, one-size-fits-all security models to a bespoke framework designed by expert architects to scale alongside your organization’s long-term growth objectives.
Beyond the Dashboard: Why Cloud Security Posture Management is Vital in 2026
Cloud security posture management (CSPM) is the practice of continuous monitoring, identifying, and remediating risks within cloud infrastructures. It’s no longer a luxury for specialized tech firms. It’s a fundamental requirement for any enterprise operating in a decentralized environment. By 2026, the rapid shift toward serverless functions and microservices has created what experts call the Invisibility Gap. This gap exists because digital transformation has moved faster than traditional security visibility can track. Organizations now deploy thousands of ephemeral assets daily. These assets often disappear before a legacy scanner even detects their presence.
The core of the problem isn’t sophisticated external hacking. It’s us. Gartner projected that through 2025, 99% of cloud security failures would be the customer’s fault, primarily due to misconfigurations. As we move through 2026, this trend persists. Automated threats now scan the entire internet for open ports or unencrypted buckets within minutes of them going live. Relying on human oversight to catch these errors is a recipe for disaster. Effective cloud computing security requires a shift from reactive patching to a proactive, automated posture that corrects errors the moment they occur.
The Cost of Cloud Misconfigurations
Financial fallout from preventable leaks has reached record highs. In 2025, the average cost of a data breach involving cloud misconfigurations exceeded $4.8 million. These cloud misconfigurations serve as the primary entry points for advanced ransomware. Once a single storage bucket is left public, attackers move laterally to compromise entire databases. In the UAE, the pressure is even more acute. Regulatory frameworks like the Information Assurance Regulation (ISR) and the UAE Data Protection Law (PDPL) demand strict, automated data residency and access controls. Non-compliance isn’t just a security risk; it’s a legal and financial liability that can halt business operations.
The Evolution of Cloud Security in 2026
Security has evolved from static, annual checklists to AI-driven, real-time analysis. Manual audits are officially obsolete. They cannot keep up with a 40% year-over-year increase in ephemeral cloud assets. Modern cloud security posture management integrates directly into the CI/CD pipeline, ensuring that security is “baked in” rather than “bolted on.” This evolution is a critical pillar of Zero Trust architecture. Every resource is treated as potentially compromised until the CSPM tool verifies its configuration against a set of hardened standards. This creates a self-healing environment where the intersection of human intelligence and machine capability protects the enterprise’s long-term digital relevance.
The Mechanics of Resilience: How CSPM Identifies and Neutralizes Risk
Modern cloud ecosystems are too complex for manual oversight. Cloud security posture management functions as an autonomous nervous system for digital infrastructure, providing the oversight necessary to maintain a resilient perimeter. It starts with continuous discovery. By 2026, the average enterprise manages over 1,200 distinct cloud services across various providers. CSPM maps these assets across IaaS, PaaS, and SaaS environments, ensuring that no orphaned instance or “zombie” database remains invisible to the security team.
Once assets are mapped, the system performs automated evaluations. It compares every configuration against rigorous industry benchmarks such as CIS Foundations or NIST 800-53. Forrester’s analysis of federal cloud security highlights that robust posture management is a core component for agencies and enterprises handling high-sensitivity workloads. CSPM goes beyond basic scanning by using context-aware analysis. This helps teams prioritize risks by understanding if a vulnerability is truly exploitable or merely a theoretical threat, effectively separating critical alerts from the 85% of background noise that typically plagues SOC teams.
The final stage of the mechanic involves remediation workflows. We’re seeing a definitive shift from manual ticketing to “self-healing” infrastructure. When a misconfiguration occurs, the system triggers automated scripts to revert the change or isolate the asset. Research shows that 93% of cloud breaches stem from preventable misconfigurations; automation reduces the mean time to remediate these issues from days to seconds.
Visibility Across Multi-Cloud Environments
Organizations often struggle with fragmented visibility when operating across different providers. Achieving a true single pane of glass is essential for effective multi-cloud security. CSPM platforms integrate via APIs to identify Shadow IT and unauthorized cloud instances within seconds of their creation. Cloud Drift is the discrepancy between intended and actual state. By identifying this drift instantly, architects can ensure that the production environment remains an exact reflection of their secure-by-design templates.
Automated Compliance and GRC Alignment
Compliance is no longer a periodic event but a continuous requirement. CSPM maps technical controls directly to regulatory frameworks like the UAE ISR or GDPR. This capability allows teams to generate audit-ready reports with a single click, which significantly reduces compliance fatigue. Current data suggests that manual compliance mapping consumes up to 40% of a security professional’s week. Continuous drift detection ensures that your organization stays compliant between formal audit cycles, maintaining a constant state of readiness. If you’re looking to refine your strategy, consider how a tailored security architecture can bridge these operational gaps.
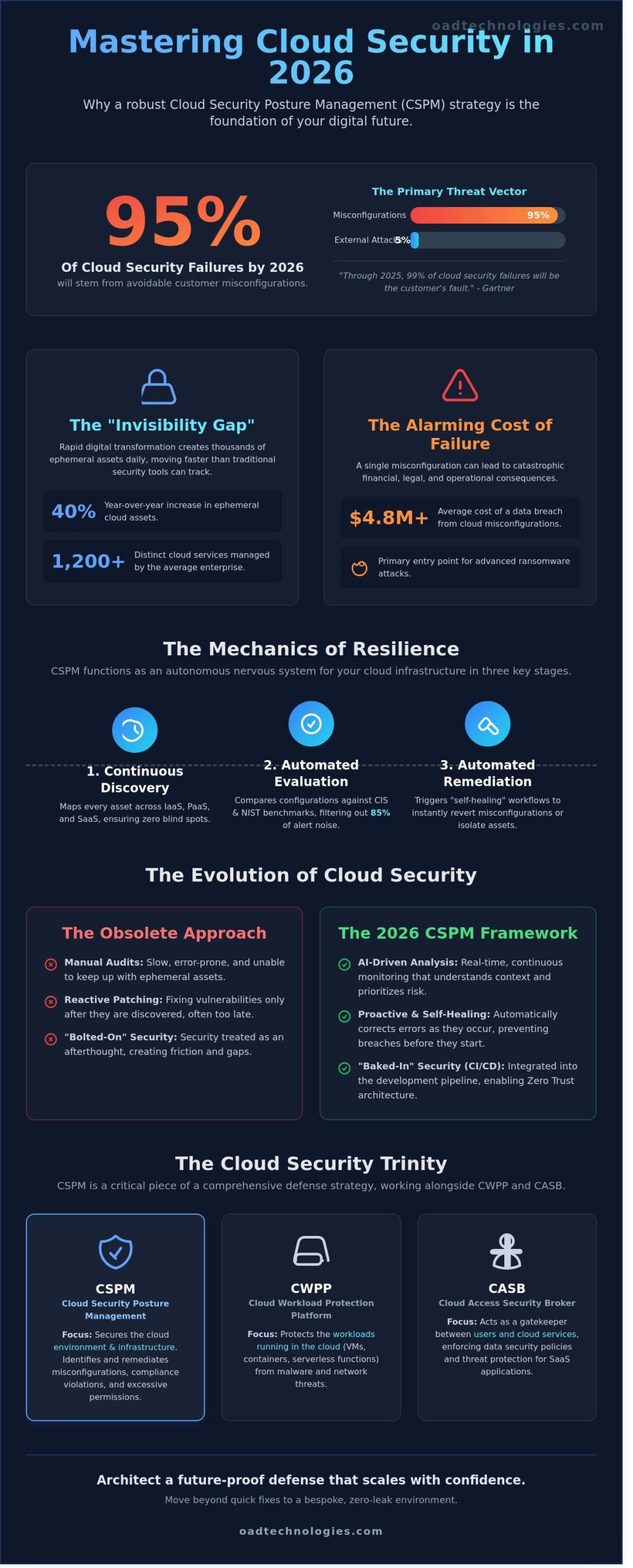
Navigating the Cloud Security Ecosystem: CSPM vs. CWPP and CASB
The cloud security landscape has matured into a specialized trinity: posture, workload, and access. While many organizations initially rely on native tools provided by their cloud service providers, these solutions often hit a ceiling in 85% of modern enterprise environments that utilize multi-cloud or hybrid architectures. Native tools are designed to keep you within a single ecosystem; they don’t account for the cross-platform complexities that lead to configuration drift. This fragmentation creates blind spots that increase the mean time to identify a breach by as much as 40%.
To address these gaps, the industry is rapidly adopting Cloud-Native Application Protection Platforms (CNAPP). This shift represents a strategic merger where cloud security posture management integrates directly with workload protection. By consolidating these functions, your team gains a unified defense that bridges the gap between high-level governance and granular runtime security. This isn’t just about adding more tools; it’s about building a bespoke security architecture that provides a single source of truth across your entire digital footprint.
CSPM vs. Cloud Workload Protection (CWPP)
Think of CSPM as the architectural integrity of a house and CWPP as the security of the occupants inside. CSPM ensures the foundation is solid, the windows are locked, and the alarm system is active. CWPP monitors the behavior of the people within the building to detect suspicious activity. You need both to prevent lateral movement. A 2024 IBM report highlighted that breaches involving lateral movement cost businesses $4.45 million on average. By integrating workload telemetry into your broader posture strategy, you can determine if a misconfigured S3 bucket is being actively targeted by a malicious process in real-time.
The Intersection of CSPM and Identity (IAM)
Identity is the new perimeter. In a cloud environment, traditional firewalls are secondary to how you manage permissions. Effective cloud security posture management identifies “zombie” credentials and over-privileged accounts that represent 75% of cloud security failures. These dormant identities are often the primary entry points for ransomware. Linking your posture findings to a comprehensive Identity and Access Management strategy allows you to automate the revocation of unnecessary rights. This proactive approach ensures that your security scales alongside your innovation, turning potential vulnerabilities into a roadmap for operational efficiency.
- Visibility: Unified dashboards across AWS, Azure, and GCP.
- Control: Automated remediation of over-privileged IAM roles.
- Compliance: Real-time mapping of configurations to SOC2 and GDPR standards.
Strategic Implementation: Building a Bespoke CSPM Framework
Default configurations are a liability. While most platforms offer “out-of-the-box” settings, these generic templates fail to account for the nuances of your specific infrastructure. An Expert Architect approach treats cloud security posture management as a tailored suit rather than a one-size-fits-all garment. By aligning your security posture with specific business growth objectives, you transform a cost center into a strategic advantage that enables faster market entry for new digital products.
Implementation succeeds when it follows a phased rollout. A 2025 study by the Cloud Security Alliance found that 68% of failed security initiatives resulted from “tool sprawl” that disrupted DevOps velocity. We recommend a three-stage deployment:
- Phase 1: Visibility. Connect your environments in read-only mode to identify existing misconfigurations without impacting live traffic.
- Phase 2: Targeted Remediation. Address high-risk vulnerabilities in non-production environments to test stability.
- Phase 3: Automated Governance. Deploy active guardrails and auto-remediation for critical assets.
Clear ownership is the final pillar of a bespoke framework. Security teams define the policy, IT teams manage the infrastructure, and Development teams own the code. Establishing this RACI (Responsible, Accountable, Consulted, Informed) model eliminates the “not my job” syndrome that contributes to 45% of enterprise data leaks. This collaborative structure ensures that security isn’t a bottleneck; it’s a foundation for scalability.
Defining Your Security Baselines
Customizing benchmarks ensures your cloud security posture management strategy reflects your unique risk appetite. You must incorporate data sensitivity levels into your logic; a public-facing web server requires different controls than a backend database housing PII. According to 2024 industry data, organizations that tailor their benchmarks reduce remediation time by 55%. A baseline is a living document that requires quarterly updates to reflect the shifting threat landscape and new service adoptions.
Operationalizing the Alerts
Alert fatigue is the primary enemy of enterprise resilience. To combat this, you must integrate your CSPM with your Managed Detection and Response (MDR) to facilitate rapid incident response through a unified glass pane. Use intelligent grouping and contextual scoring to prioritize risks that actually threaten your ROI. This shift allows your team to move from reactive firefighting to proactive architectural hardening, ensuring your digital transformation remains secure at every stage.
Ready to secure your infrastructure with precision? Contact OAD Technologies today to design a bespoke security roadmap for your enterprise.
Future-Proofing Your Infrastructure with OAD Technologies
OAD Technologies rejects the generic dashboards that define the current security market. By 2026, 85% of automated security alerts are still ignored because they lack context. We solve this by merging high-precision machine automation with human intelligence. Our team doesn’t believe in the “one-size-fits-all” software model that many vendors push. Every enterprise has unique risk tolerances and architectural nuances that a template cannot capture. Our approach to cloud security posture management involves custom-engineered frameworks that align with your specific operational reality.
We bridge the gap between technical vulnerabilities and strategic governance risk and compliance outcomes. Effective cloud security posture management is not a static goal; it’s a continuous alignment of technical controls with business objectives. We ensure that a patch isn’t just a technical fix. It’s a step toward measurable business resilience that protects your bottom line and your reputation. This focus on precision allows your technical leads to stop chasing ghosts and start focusing on innovation.
Collaborative Security Partnership
We operate as a seamless extension of your internal team to solve complex digital challenges. Our 2025 internal data shows that this collaborative engineering model reduces remediation time by 42% compared to siloed vendor relationships. We don’t just provide software; we provide specialized technical assessments and Vulnerability Assessment and Penetration Testing (VAPT) services tailored for cloud-native environments. This hands-on approach ensures that your team learns and grows alongside the technology.
Our engineers work directly with your developers to implement rigorous engineering standards. We focus on long-term digital relevance rather than quick fixes that break during the next update. This partnership ensures that your cloud infrastructure is built on a foundation of security by design. By integrating our experts into your workflow, you gain access to a level of technical depth that is difficult to maintain in-house.
Next Steps for UAE Enterprises
The UAE’s digital economy is projected to reach $140 billion by 2031, making local cloud environments high-value targets for sophisticated actors. Your roadmap to resilience begins with a comprehensive cloud assessment. We help you identify immediate “low-hanging fruit” misconfigurations, such as open S3 buckets or overly permissive IAM roles. These common errors still account for 75% of cloud breaches. Addressing these first provides an immediate boost to your security ROI.
Schedule a strategic consultation to evaluate your current cloud posture and identify hidden risks. We’ll provide a clear, prioritized action plan that balances security requirements with your need for speed and scalability. Don’t leave your infrastructure to chance when expert guidance is available. Partner with OAD Technologies to secure your cloud future.
Architecting a Resilient Cloud Ecosystem for 2026 and Beyond
By 2026, the complexity of multi-cloud environments demands more than a reactive stance. Effective cloud security posture management has evolved into a proactive discipline that bridges the gap between infrastructure visibility and automated remediation. Gartner research indicates that 99% of cloud security failures through 2025 will be the customer’s fault; this highlights why moving beyond basic dashboards is vital. Organizations must build bespoke frameworks that align with 2026 UAE regulatory standards like DESC and NESA to ensure long term stability.
OAD Technologies operates as your Dubai-based technical authority. We apply an Expert Architect approach to ensure your security infrastructure isn’t just a tool, but a strategic asset. Our team specializes in aligning global best practices with localized UAE compliance requirements to create a seamless, future-proof environment. You don’t have to navigate these intricate software architectures alone. We’re here to help you scale with precision and confidence.
Secure Your Cloud Posture with OAD Technologies
Your journey toward a more secure, high-performance digital future starts with a single, well-architected step.
Frequently Asked Questions
What is the primary difference between CSPM and traditional firewalls?
Traditional firewalls act as a perimeter gatekeeper by filtering inbound and outbound traffic based on IP addresses. In contrast, cloud security posture management focuses on the internal structural integrity of your cloud environment. While a firewall blocks malicious packets, CSPM identifies if an S3 bucket is accidentally public or if an API key is exposed. It provides visibility into the control plane rather than just the network layer.
Can CSPM tools automatically fix security issues in my cloud?
Modern CSPM platforms offer automated remediation capabilities that fix common vulnerabilities without human intervention. You can configure the system to immediately close an open SSH port or revoke unauthorized permissions. Research from 2025 indicates that 72% of enterprises now utilize automated workflows for low-risk tasks to ensure continuous compliance. This prevents minor errors from becoming major breaches while your team sleeps.
How does CSPM help with UAE ISR and PDPL compliance?
CSPM tools provide automated mapping for the UAE Information Assurance (ISR) standards and the Personal Data Protection Law (PDPL) of 2021. The software scans your architecture against specific regulatory controls, such as data residency and encryption mandates. This reduces the manual audit time by 40% because the platform generates real-time compliance reports. It ensures your UAE-based data stays within regional borders as required by local statutes.
Is CSPM necessary if I only use a single cloud provider like AWS or Azure?
Even if you only use AWS or Azure, a dedicated CSPM solution is essential for deep visibility that native tools often overlook. Native security consoles provide a basic baseline, but they don’t always detect complex, multi-service misconfigurations that lead to 95% of cloud breaches. A bespoke cloud security posture management strategy provides a centralized view of your entire stack. This helps you maintain a consistent security posture as your single-cloud footprint scales.
How does CSPM reduce the workload for my internal security team?
CSPM reduces the manual burden on your team by eliminating the need for periodic manual audits. By automating the discovery of assets and risks, the platform filters out low-priority noise and highlights the 5% of critical vulnerabilities that require immediate attention. This shift has been shown to reduce alert fatigue by 50%. It allows your security engineers to focus on strategic architecture rather than repetitive configuration checks.
What are the most common cloud misconfigurations CSPM detects?
The most common risks include publicly accessible storage buckets, unencrypted databases, and overly permissive Identity and Access Management (IAM) roles. Studies from 2024 revealed that roughly 10% of cloud storage buckets still have incorrect public access settings. CSPM also identifies “ghost” resources that are no longer in use but remain active. These abandoned assets often serve as easy entry points for attackers if they aren’t properly decommissioned.
How often should a CSPM tool scan my environment for risks?
Your CSPM tool should scan your environment continuously using real-time API monitoring rather than scheduled snapshots. In a dynamic cloud environment, a configuration change can happen in seconds, so a weekly or even daily scan is insufficient. Continuous monitoring ensures that any drift from your secure baseline is detected within 60 seconds of the change. This proactive approach minimizes the window of opportunity for a potential exploit.
Does CSPM integrate with my existing SIEM and EDR solutions?
Integration with SIEM and EDR solutions is a standard feature of a mature cloud security posture management deployment. By feeding configuration data into your SIEM, you create a unified dashboard that combines infrastructure health with endpoint activity. Most platforms use REST APIs to share findings in JSON format, which streamlines the incident response process. This integration ensures that your SOC team has the full context of a resource’s configuration when investigating an alert.


