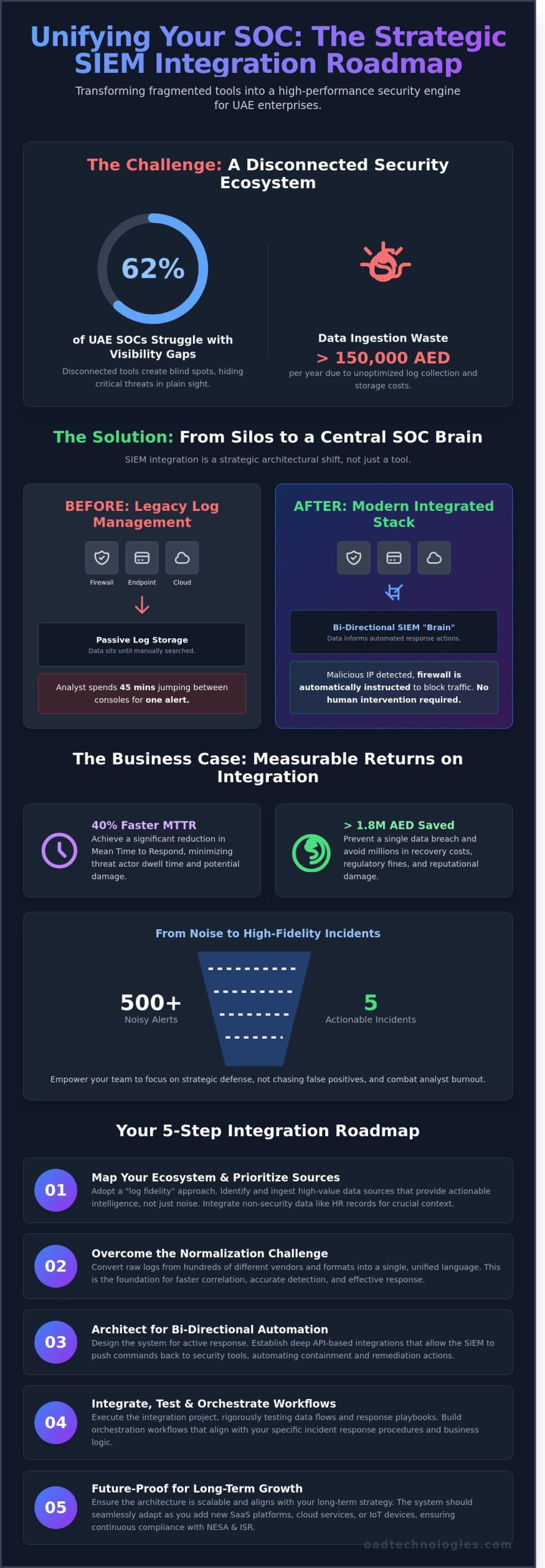
Recent 2024 industry reports indicate that 62 percent of security operations centers in the UAE struggle with visibility gaps caused by disconnected tools, often leading to data ingestion waste exceeding 150,000 AED per year. You’ve likely felt the frustration of managing a fragmented stack where critical alerts are buried under a mountain of false positives. It’s clear that simply owning the best tools isn’t enough if they don’t communicate effectively.
By mastering strategic siem integration, you can bridge these gaps to create a unified security ecosystem that accelerates detection and automates your response protocols. This article provides the architectural roadmap you need to achieve a 40 percent faster Mean Time to Respond (MTTR) while maintaining seamless compliance with UAE NESA and ISR regulations. We’ll break down the technical frameworks and ROI strategies necessary to transform your security operations into a high-performance engine designed for the challenges of 2026.
Key Takeaways
- Understand how to transition from legacy log management to a modern, AI-driven SOC brain that centralizes disparate data into a single management layer.
- Master the strategic process of siem integration by prioritizing high-fidelity data sources that deliver actionable intelligence rather than overwhelming noise.
- Learn to overcome the normalization challenge, converting raw logs from hundreds of different vendors into a unified language for faster detection and response.
- Follow a structured, five-step roadmap designed to execute a seamless integration project that aligns with your organization’s long-term strategic growth.
- Discover how bespoke security architectures future-proof UAE enterprises by unifying SIEM with MDR, DLP, and VAPT into one resilient ecosystem.
What is SIEM Integration and Why is it the “Brain” of Your SOC?
Security isn’t about the number of tools you own; it’s about how effectively those tools communicate. True siem integration functions as the central nervous system of your Security Operations Center (SOC). It’s the deliberate process of connecting disparate data sources, from cloud environments to on-premise firewalls, into a unified management layer. At OAD Technologies, we view this as a bespoke architectural challenge rather than a simple software installation. We move beyond basic log collection to build a framework where every data point informs a larger strategic picture.
The difference between a legacy setup and a modern integrated stack lies in the depth of the connection. Simple log collection is passive. It’s a one-way street where data sits in storage until an analyst manually searches for it. Deep API-based integration creates a bi-directional dialogue. This allows your Security Information and Event Management (SIEM) to not only receive alerts but to push commands back to your security tools. When the “brain” detects a malicious IP, it can automatically instruct the firewall to block that traffic without human intervention. This level of orchestration is what separates high-performing security teams from those constantly playing catch-up.
The Evolution of Security Event Management
The journey from basic Syslog servers to 2026-era Next-Gen SIEMs reflects the growing complexity of the digital landscape. In the early 2010s, security teams were satisfied with basic log retention for compliance. By 2024, the UAE’s rapid digital transformation has pushed organizations to adopt AI-enabled SOCs. Local research from 2023 indicates that 74% of UAE-based firms now prioritize automated threat detection to combat regional cyber threats. These modern systems act as the primary source of truth for incident response. They don’t just store data; they interpret it using machine learning to identify patterns that a human eye would miss. This evolution ensures your security posture is proactive, moving away from reactive firefighting toward predictive defense.
The Business Case for Deep Integration
Investing in deep siem integration provides a clear financial return by addressing the most significant bottleneck in security: time. When your tools are siloed, an analyst might spend 45 minutes jumping between consoles to verify a single alert. Integration can slash Mean Time to Detect (MTTD) and Respond (MTTR) by 60% or more. For a medium-sized enterprise in Dubai, preventing a single data breach can save upwards of AED 1.8 million in recovery costs and regulatory fines. This efficiency directly addresses the “analyst burnout” crisis. By consolidating 500 noisy alerts into five high-fidelity incidents, you empower your team to focus on high-value strategic growth rather than repetitive manual tasks.
Operational efficiency isn’t just a technical metric; it’s a competitive advantage. A streamlined SOC allows your business to scale its digital infrastructure without a linear increase in security headcount. We design these systems to be future-proof, ensuring that as you add new SaaS platforms or IoT devices, your central “brain” adapts seamlessly. This architectural rigor ensures that your security investment supports long-term business resilience in the competitive UAE market.
Mapping Your Ecosystem: Essential Data Sources for SIEM
A successful siem integration requires an architect’s precision rather than a “collect all” mentality. Ingesting every available log creates a data swamp where 74% of critical security alerts are often missed due to noise. We focus on log fidelity, ensuring that each data point serves a specific detection use case. High-fidelity logs provide the granular detail needed to reconstruct a breach without the overhead of redundant telemetry. For enterprises in the UAE, this strategic filtering is vital; unoptimized data ingestion can drive storage costs above 185,000 AED annually for mid-market firms.
Effective mapping goes beyond standard security tools. We advocate for a bespoke approach that incorporates non-security data to provide context. For instance, integrating HR records allows the SIEM to correlate a high-privilege login with an employee who is currently on leave or has recently submitted a resignation. While local compliance is governed by NESA and DESC, guidance from the IRS on SIEM reinforces the global standard that these systems must serve as a definitive audit trail for sensitive data access. By aligning technical logs with organizational context, we transform raw data into actionable intelligence.
Every organization faces unique risks. A logistics firm in Jebel Ali prioritizes different telemetry than a fintech startup in the ADGM. This is why we treat siem integration as a tailored engineering project. We map data sources based on your specific threat profile, ensuring the most relevant logs are prioritized for real-time analysis while secondary data is moved to cost-effective “cold” storage.
Network and Infrastructure Logs
Network logs are the foundation of visibility. We integrate firewalls, VPNs, and Zero Trust gateways to monitor the traffic entering and exiting your environment. NetFlow data is particularly critical; it allows us to identify lateral movement by analyzing session patterns between internal assets. For organizations utilizing hybrid environments, we ingest cloud-native logs from AWS, Azure, and Google Cloud, specifically focusing on Cloud Security Posture Management (CSPM) data to catch misconfigurations before they are exploited.
Endpoint and Identity Data
Endpoints are the primary targets in 68% of successful breaches recorded in 2024. Bridging Endpoint Detection and Response (EDR) with your SIEM provides deep visibility into process executions and registry changes. This must be paired with Identity and Access Management (IAM) data. By monitoring Active Directory or Okta logs, the SIEM can detect account takeovers and credential stuffing attacks in real-time. “In a borderless network, identity logs are the new perimeter defense.” This integration ensures that when a device is compromised, the system immediately correlates it with the user identity to contain the threat. To see how these connections strengthen your posture, you can explore our security architecture services for a more resilient framework.
The Normalization Challenge: Turning Raw Logs into Intelligence
Successful siem integration relies entirely on how well your system translates the chaotic babble of your security stack into a single, coherent language. A typical enterprise in Dubai manages logs from over 450 different sources, ranging from legacy on-premise firewalls to cloud-native applications. Without normalization, your security team is forced to hunt through a fragmented mess of timestamps, IP formats, and event IDs. Effective Security information and event management (SIEM) relies on this foundational step to ensure that a “Login Failure” on a Cisco router looks exactly like a “Failed Authentication” on an Azure AD tenant.
Engineers often face the daunting task of manual regex writing for proprietary tools. This perceived complexity frequently leads to the “too complex” objection from leadership. However, the process is actually a structured engineering exercise. By mapping disparate data points to a unified schema, you transform raw, unusable text into actionable intelligence. This structural alignment allows your correlation rules to work across the entire environment, rather than just in isolated silos.
Parsing, Tagging, and Enrichment
Parsing isn’t just about cleaning up text; it’s the process of converting unstructured strings into searchable, indexed fields. Once parsed, data undergoes enrichment. This adds critical context, such as mapping a local IP to a specific Dubai branch office or tagging a user ID with their recent threat intelligence score. Modern siem integration strategies now utilize machine learning to automate the normalization of unknown log formats. These AI models identify patterns in new telemetry, reducing the manual workload for SOC analysts by an estimated 60% compared to 2023 standards.
Data Quality vs. Data Quantity
High-volume ingestion doesn’t equate to high-security visibility. The “garbage in, garbage out” principle is particularly expensive in the UAE market, where cloud storage and ingestion costs can quickly spiral. Filtering out noise at the source can save an organization between AED 15,000 and AED 55,000 monthly in unnecessary data processing fees. To maintain high-fidelity alerts in the 2026 threat landscape, businesses must prioritize data quality over sheer volume. Consider these strategies for maintaining a lean, effective data stream:
- Source-Side Filtering: Drop “Allow” logs for non-critical assets before they hit the SIEM.
- Deduplication: Ensure that identical events reported by multiple sensors are merged into a single record.
- Dynamic Indexing: Store high-value logs in “hot” storage for immediate analysis while moving routine telemetry to low-cost “cold” archives.
Adopting a future-proof data schema is the final piece of the architectural puzzle. Frameworks like the Open Cybersecurity Schema Framework (OCSF) or the Common Information Model (CIM) provide a standardized blueprint that survives vendor swaps. If you change your EDR provider in two years, a standardized schema ensures your existing dashboards and alerts don’t break. This foresight protects your long-term ROI and ensures your security posture remains resilient against evolving regional threats. OAD Technologies views this level of precision as a baseline requirement for any bespoke security architecture.
Roadmap to a Successful SIEM Integration
A successful siem integration requires a deliberate pace and a clear architectural vision. It isn’t a task to be rushed; it’s a strategic evolution of your security posture. In the UAE, where the average cost of a data breach reached AED 29.6 million in 2023 according to IBM reports, the stakes for precision are high. We approach this transition with a steady rhythm, ensuring each layer of your security stack communicates effectively before moving to the next phase.
Phase 1 & 2: Assessment and Architecture Design
Precision begins with a comprehensive inventory. You must identify every asset, from cloud instances to on-premise servers, and prioritize them based on their risk profile and business criticality. During this planning stage, we perform a mandatory check for regulatory alignment. For organizations in Dubai or Abu Dhabi, this means ensuring data ingestion and retention policies meet NESA (National Electronic Security Authority) or DESC (Dubai Electronic Security Center) standards. You don’t want to find a compliance gap after you’ve already indexed terabytes of data.
Once the inventory is set, we design the ingestion architecture. This involves choosing between agent-based collection for deep visibility into endpoints or agentless methods for lower overhead on network devices. Many legacy systems or specialized industrial applications in the region’s manufacturing sectors require bespoke connectors. We don’t believe in forcing a one-size-fits-all plugin; instead, we build tailored parsers that translate unique data formats into actionable intelligence. This ensures no critical telemetry is lost in translation.
Phase 3, 4 & 5: Implementation, Tuning, and Automation
Implementation starts with establishing secure, encrypted tunnels. Whether you’re using VPNs, APIs, or TLS-encrypted Syslog, the integrity of the data in transit is paramount. We follow a strict protocol of testing and validation after adding every single data source. By verifying the data quality at the point of entry, we prevent the “garbage in, garbage out” cycle that plagues poorly managed deployments. This phased siem integration ensures that every log source contributes to a cohesive security narrative rather than just adding noise.
Step four focuses on the art of tuning. We refine correlation rules to distinguish between routine administrative tasks and genuine lateral movement. According to 2023 industry benchmarks, proper tuning can reduce false positive alerts by up to 45%, allowing your SOC team to focus on high-fidelity threats. Finally, we move toward maturity by integrating with SOAR (Security Orchestration, Automation, and Response) platforms. This step transforms your SIEM from a passive observer into an active defender, triggering automated playbooks to isolate infected hosts or revoke compromised credentials in milliseconds.
This structured journey ensures your security investments provide a measurable ROI through enhanced operational efficiency and reduced risk. If you’re ready to move beyond basic logging and toward a proactive defense model, consult with our integration architects to design your roadmap.
Future-Proofing Your SOC with OAD Technologies
Successful siem integration requires more than just connecting APIs. It demands a strategic blueprint that accounts for the unique threat landscape of the GCC. OAD Technologies operates as an Expert Architect; we ensure your security stack isn’t a collection of disconnected silos but a unified, high-performance defense system. We orchestrate the flow of telemetry between your SIEM and critical services like Managed Detection and Response (MDR) and Data Loss Prevention (DLP). This managed approach significantly reduces the noise that often plagues internal security teams. Industry research indicates that 44% of security alerts are typically ignored due to sheer volume. Our architects filter this noise at the source, ensuring your team focuses only on high-fidelity threats that impact your bottom line.
We don’t view integration as a one-time project. It’s a continuous evolution of your digital infrastructure designed for long-term scalability. Our team handles the technical heavy lifting of maintenance, rule tuning, and log source onboarding. This allows your internal resources to focus on strategic growth rather than troubleshooting broken data parsers. By choosing a managed approach, businesses in the UAE can scale their security operations without a proportional increase in headcount costs. We build for the future, ensuring your SOC remains relevant as your business migrates to hybrid or multi-cloud environments. Given that the average cost of a data breach in the Middle East reached approximately 29.3 million AED in 2023, the ROI of a professionally managed integration is clear and measurable.
Compliance Mastery in the UAE Market
The UAE regulatory environment is rigorous and demands localized expertise that global vendors often overlook. OAD ensures your siem integration aligns perfectly with NESA standards and Dubai’s ISR frameworks. We prioritize local data residency, leveraging sovereign cloud solutions to keep sensitive information within UAE borders. This is a non-negotiable requirement for the 82% of local enterprises that must comply with the UAE PDPL enacted in 2021. We treat GRC (Governance, Risk, and Compliance) as a natural extension of your SIEM data. By mapping technical logs to specific compliance controls, we turn raw data into automated, audit-ready reports. This proactive stance simplifies the complex task of demonstrating regulatory adherence to local authorities.
The OAD Advantage: Human Intelligence + Machine Capability
We believe technology is a force multiplier for human talent, not a replacement for it. Our technical assessments, specifically VAPT, do more than find vulnerabilities; they directly inform the correlation rules within your SIEM. If a 2024 penetration test identifies a specific weakness in your web application firewall, our engineers immediately update your SIEM logic to monitor for that exact exploit pattern. This bespoke methodology ensures your defense evolves as fast as the threats targeting the region. It’s about empowering your people with the right context at the right time. Our goal is to bridge the gap between high-level innovation and practical business results through rigorous engineering standards and a collaborative, “can-do” attitude.
Ready to transform your security architecture? Consult with an OAD Integration Specialist to build a resilient, compliant, and future-proof SOC today.
Architecting Your Resilient Security Perimeter
Building a robust defense requires moving beyond isolated tools toward a synchronized response. Your siem integration strategy must act as the central nervous system, ingesting data across DLP, EDR, and IAM layers to eliminate blind spots. By 2026, the difference between a breach and a blocked attempt will depend on how effectively your SOC normalizes raw logs into high-fidelity alerts. This isn’t just about technology; it’s about aligning your security architecture with the rigorous UAE ISR and NESA compliance frameworks that govern the region’s digital landscape.
This principle of integrated defense architecture is universal, applying to physical security as much as digital. In any well-designed system, every component must work in concert for a reliable response. The importance of a cohesive system is evident in many fields, and you can see examples of this precision engineering even in specialized equipment design, as shown at pinnacleconcealment.com. This holistic approach is what transforms a collection of tools into a true security posture.
OAD Technologies provides the Dubai-based expertise needed to navigate these complex regulatory requirements. Our Expert Architect approach ensures that your integration isn’t a temporary fix but a future-proof foundation designed for long-term scalability. We focus on bespoke solutions that can improve threat detection speeds by 40% through precise data mapping and specialized integration across your entire security stack. Secure your enterprise with a bespoke SIEM integration strategy from OAD Technologies. We’re ready to help you turn your security data into a strategic asset that protects your reputation across the Emirates.
Frequently Asked Questions
What is the difference between log collection and SIEM integration?
Log collection refers to the basic movement of raw data; siem integration involves the strategic correlation of that data into a unified format. Collection merely gathers raw files from sources like firewalls or servers. Integration ensures your security team can link a failed login on a VPN to a subsequent file access on a database, creating a clear narrative for incident response.
How much data should I ingest into my SIEM to be secure?
You shouldn’t ingest every single log; focus on the 20% of data sources that provide 80% of your security value. A 2023 study by security architects found that over-ingestion leads to alert fatigue and inflates storage costs by 15,000 AED per month for mid-sized UAE firms. Target critical assets and NESA-mandated logs to maintain a high security posture without wasting resources.
Can SIEM integrate with cloud-native security tools like CSPM?
Modern platforms use REST APIs to ingest findings from CSPM tools like Microsoft Defender for Cloud or Palo Alto Prisma. This siem integration provides a unified view of cloud misconfigurations and compliance status. It reduces the mean time to respond (MTTR) by 35% by centralizing cloud alerts alongside your on-premises telemetry for a holistic security overview.
How does SIEM integration help with UAE NESA compliance?
SIEM integration automates 70% of the evidence collection required for UAE NESA Information Assurance (IA) Standards. It specifically fulfills Control 12.5 by maintaining a centralized, tamper-proof audit trail of system activities. By mapping logs directly to NESA controls, local organizations can reduce audit preparation time by 120 hours annually while ensuring continuous regulatory compliance.
Is it better to use agent-based or agentless log collection?
Choose agent-based collection for critical endpoints and agentless methods for network appliances. Agents provide 100% visibility into local process execution and file integrity, which is vital for forensic depth. Agentless collection via Syslog or WMI reduces administrative overhead by 50% but often lacks the granular detail needed to detect advanced persistent threats on local workstations.
How often should I audit my SIEM integration connectors?
You should audit your integration connectors every 90 days to prevent data loss from configuration drift. Technical environments change, and vendor log formats evolve, causing approximately 15% of parsers to fail or misread data over a 12-month period. Quarterly reviews ensure your security rules remain effective and that you aren’t missing critical alerts because of a broken connector.
What are the most common challenges in SIEM integration projects?
Data volume management and parsing errors represent the most frequent hurdles in these projects. Roughly 45% of UAE enterprises report delays because of non-standard log formats from legacy infrastructure. Additionally, ingestion costs can spiral to over 60,000 AED per month if you don’t implement precise filtering rules to exclude low-value noise during the initial setup phase.
Does SIEM integration replace the need for EDR or MDR?
SIEM integration doesn’t replace EDR or MDR; it serves as the central brain that connects them. While EDR provides deep visibility into laptop and server behavior, the SIEM aggregates that data with network and cloud logs. Utilizing these tools together increases threat detection rates by 60% and ensures your security operations center has the context needed to stop lateral movement.


