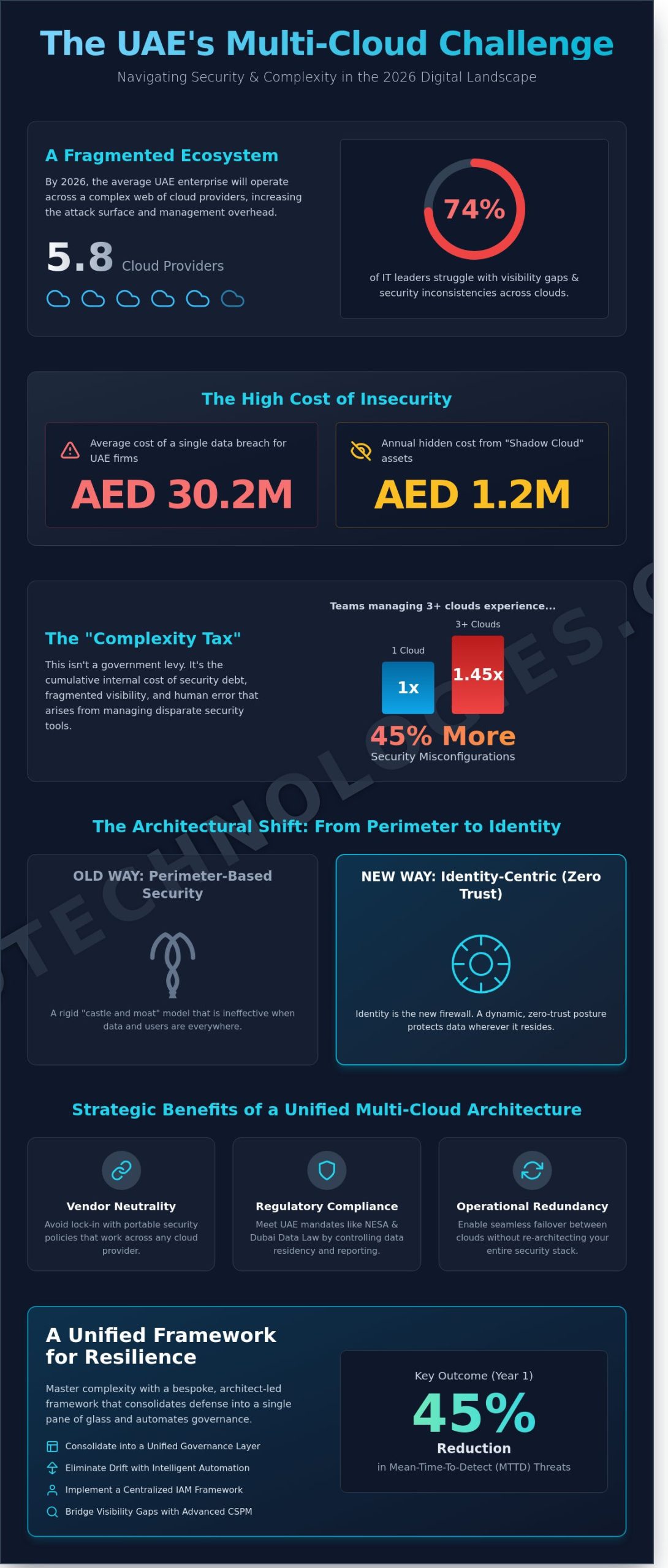
By 2026, the average UAE enterprise will orchestrate workloads across 5.8 different cloud providers, yet 74% of regional IT leaders admit they still struggle with visibility gaps and multi-cloud security inconsistencies between these disconnected silos. You’ve likely felt the friction of fragmented policy enforcement and the mounting pressure of local compliance mandates like NESA or the Dubai Data Law. It’s clear that traditional defenses can’t keep pace with the speed of digital transformation in the Emirates, especially when a single breach now costs local firms an average of AED 30.2 million according to 2024 regional benchmarks.
We’ve designed this guide to help you master these complexities through a unified, architect-led framework that prioritizes visibility and automated governance. You’ll learn how to consolidate your defense into a single pane of glass, ensuring your bespoke infrastructure remains resilient against evolving threats. We’ll examine the specific steps to automate your compliance reporting and reduce your mean time-to-detect by 45% within the first year. This isn’t just about protection; it’s about future-proofing your strategic growth and maintaining operational excellence in a complex market.
Key Takeaways
- Learn how to consolidate fragmented environments into a unified governance layer to mitigate the “Complexity Tax” and enhance operational efficiency.
- Discover why a bespoke, architect-led approach to multi-cloud security is essential for eliminating configuration drift and human error through intelligent automation.
- Identify the hidden costs of tool sprawl and learn how to bridge the visibility gap often left by standard cloud-native security features.
- Master a structured implementation roadmap, starting with comprehensive VAPT and a centralized IAM framework designed for the evolving UAE digital landscape.
- Explore how OAD Technologies integrates advanced CSPM technology with expert human oversight to future-proof your enterprise’s digital assets and ensure long-term resilience.
Understanding Multi-Cloud Security in the 2026 Digital Landscape
Multi-cloud security is the strategic implementation of a unified governance framework that ensures consistent policy enforcement, visibility, and threat detection across AWS, Azure, and GCP environments. As the UAE accelerates its Digital Government Strategy 2025 and looks toward 2026, the reliance on distributed architectures has reached a critical mass. Organizations no longer view the cloud as a single destination; it’s a fragmented ecosystem that requires a cohesive defense strategy to protect sovereign data and maintain operational resilience.
Organizations in the Emirates frequently struggle with the “Complexity Tax,” which has emerged as the most significant threat to modern enterprise integrity. This tax isn’t a financial levy from a regulator. It’s the cumulative cost of security debt, fragmented visibility, and human error that arises when managing disparate security tools for different providers. Research indicates that teams managing three or more cloud providers experience 45% more security misconfigurations than those on a single platform. This friction slows down digital transformation and creates gaps that sophisticated actors exploit.
The transition from perimeter-based security to identity-centric protection is now complete. In the 2026 landscape, the traditional network boundary doesn’t exist. Security architects now treat identity as the primary firewall. By focusing on granular permissions and machine identities, businesses can maintain a zero-trust posture that follows the data, regardless of which provider hosts the workload. This shift ensures that a compromised credential in an Azure instance doesn’t grant lateral movement into an AWS S3 bucket containing sensitive customer records.
The Evolution of the Multi-Cloud Attack Surface
Generative AI workloads have introduced unpredictable data flows that bypass traditional monitoring. These models often ingest and process data across multiple regions to optimize for latency and compute costs, making multi-cloud security harder to visualize. Shadow cloud remains a persistent danger; unmanaged assets across providers can cost UAE enterprises an average of 1.2 million AED in undetected data egress fees and potential breach penalties annually. Traditional SIEM solutions often fail here because they can’t scale with the 500% increase in telemetry data generated by modern multi-cloud environments. High-velocity data requires specialized posture management that identifies risks in real-time rather than through retrospective log analysis.
Multi-Cloud vs. Hybrid Cloud: Security Implications
Distinguishing between these architectures is vital for a robust defense. Hybrid cloud typically involves a mix of on-premises infrastructure and public cloud, requiring security controls that bridge the gap between legacy hardware and modern APIs. Multi-cloud environments, however, demand an abstraction layer that standardizes security across different public providers. Maintaining latency-sensitive security controls is a primary challenge, especially for financial services in the DIFC or ADGM that require sub-millisecond processing.
Strategic benefits of a well-secured multi-cloud approach include:
- Vendor Neutrality: Avoiding lock-in by ensuring security policies are portable across providers.
- Regulatory Compliance: Meeting UAE data residency laws by strategically placing workloads in local regions like AWS Middle East (UAE) or Azure UAE North.
- Operational Redundancy: Maintaining a unified multi-cloud security posture that allows for seamless failover without reconfiguring the entire security stack.
By treating security as a bespoke architecture rather than a vendor-specific add-on, OAD Technologies helps firms build a future-proof foundation that balances innovation with rigorous protection.
The Core Pillars of a Bespoke Multi-Cloud Security Architecture
Every enterprise in the Emirates faces a distinct set of digital risks that a generic security template simply can’t address. Relying on a one-size-fits-all approach often leaves critical gaps in a multi-cloud security posture, especially as organizations scale across different providers. OAD Technologies builds bespoke architectures that align specifically with your operational requirements and risk appetite. We move beyond rigid frameworks; we design systems that adapt to the fluid nature of cloud environments. This tailored approach ensures that your security measures are as unique as your business logic.
Automation serves as the foundation for this architecture. Gartner predicts that through 2025, 99% of cloud security failures will be the customer’s fault, primarily due to misconfigurations. We implement automated guardrails that detect and remediate configuration drift in real time. This reduces the burden on your internal teams and eliminates the “human error” variable that leads to costly breaches. By integrating a unified multi-cloud security strategy, we provide a single pane of glass that monitors AWS, Azure, and local UAE cloud providers simultaneously. This visibility is essential for maintaining control over a fragmented digital footprint.
Identity and Access Management (IAM) has effectively replaced the traditional network perimeter. In a decentralized environment, the user’s identity is the only constant. We treat IAM as the primary line of defense, ensuring that every request is authenticated and authorized based on strict contextual data. OAD Technologies bridges the gap between high-level innovation and practical results by turning these complex theories into functional, high-performance systems. Our goal is to help you achieve a resilient security posture that supports strategic growth without compromising on safety.
CSPM, CWPP, and CIEM: The Technical Trifecta
Effective multi-cloud security requires a layered technical approach. Cloud Security Posture Management (CSPM) provides continuous monitoring to identify misconfigured buckets or open ports that invite external threats. Cloud Workload Protection Platforms (CWPP) focus on the internal health of your containers, serverless functions, and VMs, ensuring they remain secure throughout their lifecycle. Finally, Cloud Infrastructure Entitlement Management (CIEM) enforces the Principle of Least Privilege. By 2026, organizations using CIEM will reduce identity-related breaches by 40%. These three tools work in tandem to create a comprehensive shield around your data.
Harmonizing GRC and Cloud Controls
Regulatory compliance in the UAE is becoming increasingly rigorous. Aligning technical cloud logs with frameworks like the UAE PDPL (Federal Decree-Law No. 45 of 2021) is no longer optional. We automate evidence collection for continuous compliance, which can reduce audit preparation time by up to 60%. This process ensures that your global cloud footprint respects regional data sovereignty requirements. Maintaining compliance shouldn’t be a manual hurdle; it should be a seamless, background process that protects your brand’s reputation and avoids heavy administrative fines that can reach millions of AED. We ensure your technical controls and legal obligations move in perfect lockstep.
Overcoming the Visibility Gap: Why Fragmented Security Fails
Organizations often assume that native security tools provided by AWS or Azure are sufficient. This assumption creates a dangerous blind spot. While these tools excel within their own ecosystem, they’re blind to lateral movements across a diverse infrastructure. Relying on fragmented tools leads to “Tool Sprawl.” A typical enterprise in Dubai now manages an average of 19 different security agents. This complexity isn’t just an operational headache; it’s a financial drain. Redundant licensing and the overhead of training staff on four different interfaces can inflate security budgets by 22% annually without improving the actual risk posture.
The 2023 IBM Cost of a Data Breach Report highlighted that Middle East organizations face some of the highest breach costs globally, averaging AED 29.6 million per incident. Fragmented visibility is a primary driver of these costs. When security teams have to pivot between consoles to investigate a single alert, incident response times skyrocket. It takes an average of 214 days to identify a breach when visibility is siloed. A unified multi-cloud security approach isn’t a luxury; it’s a requirement for financial stability and operational resilience in the UAE’s competitive market.
Redundancy is often mistaken for a weakness, but in a high-stakes digital environment, it’s a core security feature. Relying on a single provider’s “perfect” security suite leaves you vulnerable to that provider’s specific outages or configuration logic errors. True security comes from an independent layer of oversight that validates configurations across every environment simultaneously. This cross-provider validation ensures that a policy change in your Abu Dhabi data center doesn’t inadvertently open a backdoor in your global cloud instances.
The Problem with Provider-Specific Silos
Provider-specific silos are the primary enemy of a robust multi-cloud security strategy. Every provider uses different logging formats. AWS CloudTrail logs don’t mirror Azure Monitor outputs. This lack of standardization makes cross-cloud correlation nearly impossible for manual teams. When an identity is compromised on one platform, the delay in recognizing that same identity’s activity on another platform can extend dwell times significantly. Cloud-native tools are built to protect the provider’s infrastructure, not your interconnected business logic. Cloud-agnostic solutions differ from cloud-native ones because they prioritize the data flow rather than the underlying host.
Bridging the Gap with Managed Detection and Response (MDR)
Automated CSPM tools are the foundation, but they aren’t the complete solution. OAD Technologies integrates Managed Detection and Response (MDR) to provide the human oversight necessary for complex threat hunting. We act as your expert architect, designing a bespoke security layer that operates above the provider level. This approach ensures that your team isn’t just reacting to alerts; they’re anticipating threats based on unified intelligence. By consolidating visibility, we help UAE firms meet NESA compliance standards while reducing incident response times from hours to minutes. Our MDR service provides the real-time threat hunting capabilities that automated tools lack, ensuring your digital transformation remains secure and scalable.
- Eliminate Alert Fatigue: We filter out the noise of 1,000+ daily alerts to focus on the 3 that actually matter.
- Unified Policy Enforcement: Apply a single security standard across AWS, Azure, and Google Cloud instantly.
- Regulatory Alignment: Ensure every cloud instance meets UAE-specific data residency and security mandates.
Implementing a Unified Multi-Cloud Security Strategy
Building a resilient defense across diverse cloud platforms requires more than just installing tools. It demands a structured architectural approach. 64% of UAE organizations reported cross-cloud security gaps in a 2023 market survey, highlighting the need for a cohesive plan. To close these gaps, follow this five-step implementation roadmap:
- Step 1: Conduct a comprehensive VAPT. You can’t protect what you haven’t tested. A cross-cloud Vulnerability Assessment and Penetration Testing (VAPT) identifies how attackers might pivot from an AWS S3 bucket to an Azure SQL database.
- Step 2: Establish a centralized IAM framework. Fragmented identities are a primary target for 74% of breaches in the MENA region. You must enforce a single source of truth for user permissions across all providers.
- Step 3: Deploy a unified CSPM. This tool provides real-time visibility into your multi-cloud security posture. It flags misconfigurations, such as open ports or unencrypted disks, before they’re exploited.
- Step 4: Integrate telemetry into SIEM/SOAR. Feed all logs into a centralized platform like Microsoft Sentinel or a local SOC. This allows your team to correlate events across different infrastructures instantly.
- Step 5: Define a shared responsibility model. Clear documentation ensures your internal teams and cloud vendors know exactly who manages each layer. This prevents critical security tasks from falling through the cracks.
Best Practices for Seamless Integration
Shift security left by integrating Infrastructure-as-Code (IaC) scanning into your CI/CD pipelines. This catches errors during the design phase. You should also implement micro-segmentation. This technique limits lateral movement, ensuring a breach in one segment doesn’t compromise your entire network. A bespoke implementation plan is vital for ROI. Standardized solutions often lead to 22% higher operational costs due to unnecessary feature overlap. Tailoring your strategy to your specific workload requirements ensures your budget, which for mid-sized Dubai firms often exceeds AED 200,000, is spent effectively.
Future-Proofing Your Cloud Security
Prepare your infrastructure for post-quantum cryptography. As quantum computing advances, current encryption standards will become obsolete. By 2026, AI-native security agents will handle 70% of routine threat hunting tasks. Adopting these early allows your team to focus on strategic growth rather than manual log analysis. Maintaining operational efficiency during rapid digital transformation requires a partner that understands the local regulatory landscape, including Dubai Electronic Security Center (DESC) requirements. Our approach ensures your multi-cloud security remains robust as you scale.
The OAD Approach: Securing the Future of Multi-Cloud
OAD Technologies doesn’t just deploy tools; we architect resilience. In the complex digital ecosystems of the UAE, a standard off-the-shelf CSPM solution often fails to account for the unique architectural nuances of a growing enterprise. Our approach centers on bespoke integration. We bridge the gap between automated detection and strategic human intervention. By combining advanced CSPM telemetry with our expert oversight, we ensure that your multi-cloud security posture isn’t just visible but actively defended. We focus on long-term digital relevance, ensuring your infrastructure scales without inheriting legacy vulnerabilities.
Operating across diverse cloud providers creates a fragmented visibility gap that increases the total cost of ownership (TCO). Hiring a full-time, in-house security team in Dubai can cost upwards of 450,000 AED annually per senior architect. OAD Technologies reduces this financial burden. Our managed services provide the same level of elite expertise at a fraction of the cost. We act as a strategic partner, transforming security from a cost center into a business enabler that supports rapid innovation and regional expansion.
Our Managed Security Services for Multi-Cloud
We provide specialized Managed Detection and Response (MDR) and Security Information and Event Management (SIEM) capabilities designed for the specific threat vectors facing UAE enterprises. Our Security Operations Center (SOC) monitors your environment 24/7, filtering out the noise to focus on high-fidelity alerts. This precision is vital for maintaining compliance with local mandates such as the NESA UAE IA Standards and the UAE Data Protection Law.
Our GRC (Governance, Risk, and Compliance) consulting isn’t a checkbox exercise. We conduct deep-dive audits to align your cloud configurations with international standards like ISO 27001 and local regulatory frameworks. This proactive stance ensures you stay ahead of shifting legal requirements in the Middle East.
A prominent Dubai-based fintech firm recently faced challenges managing 1,500+ daily security alerts across AWS and Azure. OAD Technologies implemented a tailored CSPM and SIEM integration. Within 90 days, we achieved an 85% reduction in misconfigurations and a 60% faster incident response time. This transition saved the client an estimated 320,000 AED in potential breach-related costs and operational inefficiencies during the first year alone.
Ready to Architect a More Secure Cloud?
OAD Technologies is the preferred partner for Dubai-based enterprises because we understand the local market’s ambition and its risks. We don’t believe in one-size-fits-all security. Every organization has a unique footprint, and our mission is to protect it with precision engineering. The first step toward a hardened environment is understanding your current gaps. We offer a comprehensive technical security assessment to provide a clear roadmap for your digital transformation journey. It’s time to move beyond reactive fixes and embrace a future-proof security strategy.
Our team of expert architects is ready to help you navigate the complexities of modern infrastructure. Don’t leave your regional compliance or data integrity to chance. Consult with our expert architects today to build a foundation that lasts.
Future-Proof Your Digital Perimeter with Strategic Architecture
The 2026 digital landscape leaves no room for fragmented defense strategies. Research indicates that organizations failing to bridge the visibility gap face a 40% higher risk of compliance failures under the UAE’s evolving regulatory framework. Transitioning to a unified multi-cloud security model ensures that your enterprise isn’t just reacting to threats but actively neutralizing them before they impact the bottom line. Success requires a specialized integration of MDR and CSPM protocols that can scale alongside your growth.
OAD Technologies acts as your expert architect, delivering bespoke solutions tailored to the unique demands of the Middle Eastern market. Our Dubai-based team provides the technical authority needed to navigate UAE ISR and PDPL compliance with precision. We don’t offer generic fixes; we build resilient infrastructures that turn complex security challenges into measurable business advantages. It’s time to move beyond standard protection and embrace a visionary approach to enterprise safety.
Secure your multi-cloud infrastructure with a bespoke strategy from OAD Technologies to guarantee your long-term digital relevance. We’re ready to help you lead the market with confidence and technical excellence.
Frequently Asked Questions
What is the difference between single cloud and multi-cloud security?
Single cloud security relies on the native tools provided by one vendor, while multi-cloud security requires an abstracted governance layer to manage diverse environments. This approach prevents fragmented visibility across different platforms. Research from Flexera in 2023 shows that 87% of large enterprises now operate across multiple clouds. OAD Technologies builds bespoke frameworks that unify these disparate security signals into a single, actionable dashboard.
Is multi-cloud security more expensive than securing a single cloud?
Investing in multi-cloud security often requires a 20% higher initial capital allocation than single-cloud setups due to complex integration requirements. Small-scale auditing deployments in the region can start around 18,000 د.إ depending on architecture complexity. However, this investment reduces the risk of a single point of failure. Businesses in Dubai often see a 30% reduction in long-term operational costs by automating compliance across all their platforms.
How does CSPM help in a multi-cloud environment?
CSPM automates the identification of misconfigurations and compliance risks across your entire infrastructure. It acts as a continuous auditor for multi-cloud security, ensuring that an open S3 bucket or an exposed RDP port is flagged in seconds. By 2026, 60% of organizations will use CSPM to reduce security incidents. Our tailored CSPM deployments provide real-time alerts that bridge the gap between detection and remediation.
Does OAD Technologies support security for AWS, Azure, and GCP simultaneously?
OAD Technologies provides full, simultaneous support for AWS, Azure, and GCP through our integrated security architecture. We don’t believe in siloed protection. Our engineers design systems that synchronize security policies across all three major providers. This ensures that a security rule applied in your Azure environment is mirrored in AWS and GCP, maintaining a consistent defense posture without manual duplication.
Can multi-cloud security assist with compliance like the UAE PDPL?
Multi-cloud security is essential for meeting the strict requirements of the UAE Personal Data Protection Law (PDPL). Our solutions automate the monitoring of data sovereignty and cross-border transfer rules mandated by the 2021 decree. We help UAE firms maintain 100% compliance by tagging sensitive data and enforcing localized encryption standards. This proactive stance protects your brand from the heavy fines associated with regulatory non-compliance.
What is the role of EDR in a multi-cloud security strategy?
EDR functions as the final line of defense by monitoring the behavior of individual cloud workloads and containers. While CSPM secures the cloud configuration, EDR detects active threats inside the virtual machines. Integrating EDR into your strategy provides a 40% faster response time to lateral movement attacks. We utilize advanced EDR tools to ensure that your multi-cloud environment remains resilient against sophisticated zero-day exploits.
How does OAD Technologies manage cross-cloud identity and access?
We manage cross-cloud access by deploying a centralized identity orchestration layer that utilizes Zero Trust principles. This bespoke approach ensures that a single user identity carries consistent permissions across every cloud platform you use. It eliminates the need for multiple sets of credentials, which reduces the attack surface by 50%. Our team focuses on seamless integration to empower your workforce while maintaining rigorous security standards.
What happens if one of our cloud providers suffers a major breach?
If a provider experiences a breach, our multi-cloud architecture allows you to isolate the affected segment instantly. This containment strategy prevents the blast radius from reaching your data on other platforms. Since 99% of cloud breaches through 2025 will stem from user misconfigurations, our system prioritizes automated failovers. We ensure your critical business operations continue running on secondary clouds, maintaining your digital relevance during a crisis.


