By 2025, Gartner predicts that 75% of security failures will stem from the inadequate management of identities, access, and privileges. This shift effectively moves the security perimeter from the network edge to the individual user, making identity and access management the most critical layer of your defense strategy. In the UAE, where digital transformation is accelerating at a 12% annual rate, the traditional approach to securing credentials is no longer sufficient to protect high-value assets.
You’ve likely struggled with the friction caused by poorly implemented MFA or the sheer complexity of managing non-human identities across fragmented cloud silos. It’s a common pain point for leaders who need to balance rigorous security with operational speed. This article delivers a strategic framework to master these complexities using a bespoke, zero-trust architectural approach. We’ll provide a clear roadmap for achieving UAE PDPL compliance and reducing the risk of credential-based attacks; ensuring your workforce remains empowered and your digital ecosystem stays resilient through 2026.
Key Takeaways
- Transition from outdated perimeter-based security to a modern strategy where identity serves as the core defensive boundary for UAE enterprises.
- Explore the four structural pillars of a resilient identity and access management framework that harmonizes machine capability with strategic human oversight.
- Prepare for the 2026 shift by learning to manage the surge of non-human identities and defending against sophisticated AI-driven access threats.
- Implement a step-by-step roadmap to transition from fragmented security silos to a unified, Zero Trust identity fabric.
- Discover how a bespoke architectural approach ensures your security infrastructure is future-proofed and precisely aligned with your specific business objectives.
Defining Identity and Access Management (IAM) in the Modern Enterprise
Security frameworks in the UAE have shifted from physical barriers to digital gatekeeping. Identity and access management (IAM) functions as the essential security discipline that ensures the right entities gain access to the right resources at the right time for the right reasons. It’s no longer enough to guard a server room in Dubai Internet City; organizations must now manage thousands of fragmented identities across cloud, on-premise, and hybrid environments. This discipline provides the structural integrity needed to verify that a user is who they claim to be and that their level of authorization matches their current operational requirements.
Traditional security relied on a perimeter-based “castle and moat” strategy. This model assumed that anything inside the network was safe. That logic fails when 74% of all data breaches involve a human element, including social engineering or credential misuse. We’ve moved into a reality where identity is the perimeter. Every login attempt, whether from a remote office in Abu Dhabi or a third-party vendor in London, represents a potential entry point. Modern identity and access management replaces static, one-time checks with dynamic, risk-based authorization. If a user’s behavior deviates from their established baseline, the system automatically adjusts permissions or requests additional verification in real-time.
OAD Technologies advocates for a Bespoke Identity Architecture. We don’t believe in the generic, one-size-fits-all templates that leave gaps in your defense. A bespoke approach means your IAM framework is engineered to fit your specific organizational hierarchy and regulatory obligations, such as the UAE’s NESA standards. By aligning technical controls with your unique business logic, we transform security from a restrictive barrier into a strategic catalyst for growth.
The Evolution of Identity: From Passwords to Biometrics
The journey of authentication has moved rapidly beyond the simple alphanumeric password. Static credentials are the weakest link in the chain; 81% of hacking-related breaches leverage stolen or weak passwords. We’ve seen a transition toward passwordless authentication and behavioral biometrics that analyze typing speed, touch pressure, and device orientation. Legacy IAM systems often fail in 2026’s sophisticated threat environment because they can’t process these high-velocity data points. OAD Technologies bridges this gap by integrating modern innovation into your existing infrastructure, ensuring your legacy systems don’t become a liability while you scale.
IAM as the Foundation of Zero Trust
A Zero Trust model is impossible to build without a robust IAM framework. You can’t implement the “Never Trust, Always Verify” principle if you don’t have total visibility into your identity lifecycle. Every request for access must be authenticated, authorized, and continuously validated based on all available data points. This level of scrutiny protects sensitive assets and ensures that lateral movement by an attacker is nearly impossible. For a deeper look at how these principles align with leadership goals, explore our guide on Zero Trust Architecture: An Introduction for Leaders. In the UAE market, where the average cost of a data breach has climbed to over AED 29 million, investing in a verified identity foundation isn’t just a technical choice; it’s a vital financial safeguard for the enterprise.
The Four Pillars of a Strategic IAM Framework
Building a resilient identity and access management framework requires more than just installing a suite of tools; it demands a sophisticated architecture where human oversight and machine precision converge to protect digital assets. At OAD Technologies, we view these pillars as a strategic partnership between your business objectives and the underlying technology. This approach ensures your infrastructure scales while remaining secure against evolving threats. By 2025, 70% of organizations will implement context-aware access policies to mitigate unauthorized entry, making a structured framework essential for long-term digital relevance.
Identity Governance and Administration (IGA)
Identity Governance and Administration (IGA) is the audit and policy engine of the identity lifecycle. It focuses on the governance aspect by managing policies, access certifications, and the Principle of Least Privilege. In the UAE, robust IGA is a regulatory necessity. Since the UAE Data Protection Law (PDPL) came into force in early 2022, organizations must demonstrate strict control over personal data. IGA provides the evidentiary trail needed for compliance, reducing the risk of the substantial fines associated with data mishandling. It automates the provisioning and de-provisioning of users, ensuring that a former employee’s access is revoked the moment they leave the company.
Access Management and SSO
Access management balances security with a frictionless user experience. Single Sign-On (SSO) and Multi-Factor Authentication (MFA) are the primary tools here, allowing users to access multiple applications with one set of credentials while adding a critical layer of verification. Modern systems go beyond static passwords. Adaptive access uses context, such as a user’s geolocation in Dubai or the health of their specific device, to make real-time decisions. This methodology aligns with a Zero Trust Architecture, where trust is never assumed and must be verified at every step. Implementing these bespoke access controls reduces help desk tickets related to password resets by up to 40%, directly improving operational efficiency.
Privileged Access Management (PAM)
If IGA and SSO handle the general workforce, Privileged Access Management (PAM) protects the “keys to the kingdom.” Technical leads and administrators often hold credentials that could bypass standard security protocols. PAM provides session monitoring and just-in-time (JIT) access, ensuring elevated permissions are only granted for a specific window of time and for a specific task. For a firm managing infrastructure assets valued at 50 million AED, a single compromised admin account could be catastrophic. PAM acts as the ultimate safeguard by isolating highly sensitive accounts from the rest of the network, preventing lateral movement by attackers.
Managing these complex systems requires a partner who understands the intersection of human intelligence and machine capability. At OAD Technologies, we act as the expert architect for your digital transformation, ensuring your identity and access management strategy is future-proof and aligned with global standards. We don’t believe in one-size-fits-all approaches; instead, we offer tailored IAM solutions that bridge the gap between high-level innovation and practical business results.
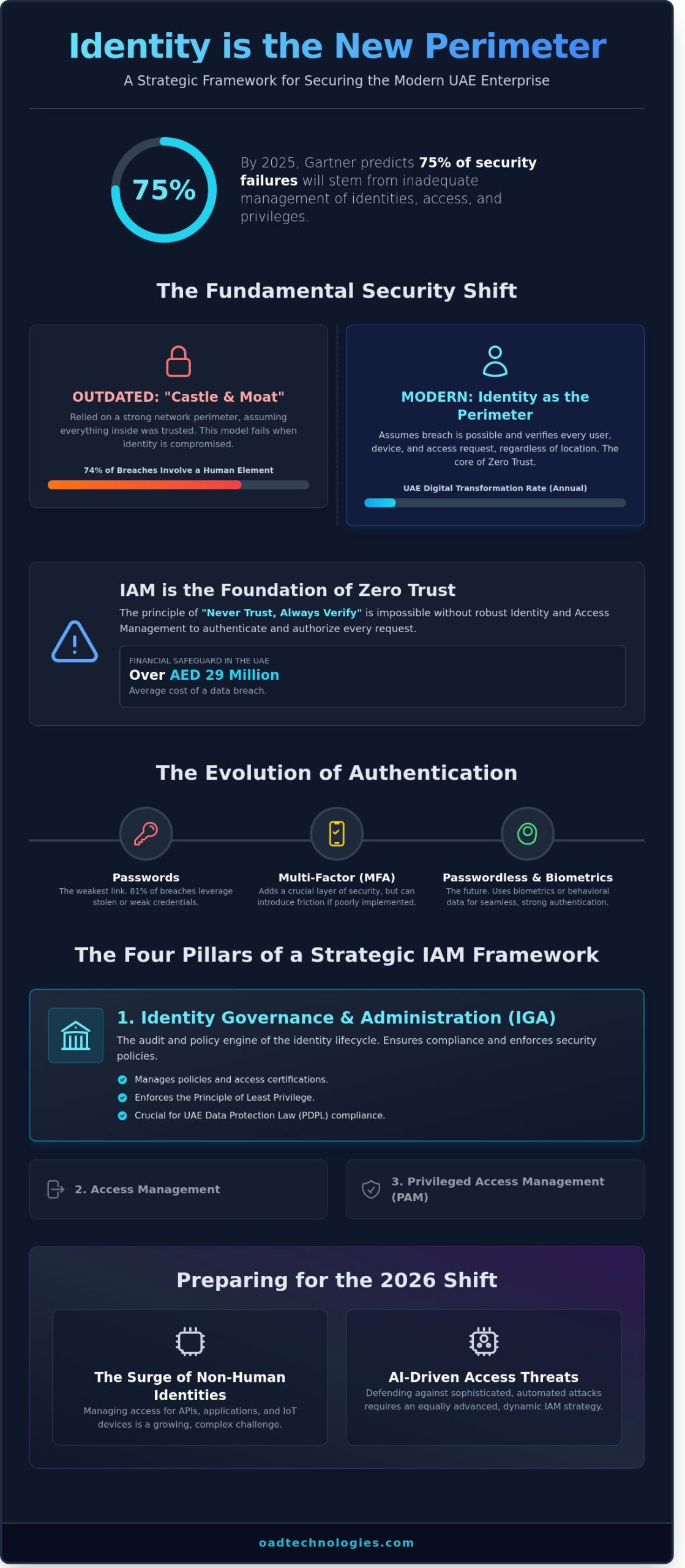
The 2026 Shift: Managing Machine Identities and AI-Driven Access
By 2026, the identity landscape in the UAE will undergo a structural transformation. Organizations in Dubai and Abu Dhabi no longer focus solely on human users; they now govern an ecosystem where machine identities outnumber human employees by a ratio of 45 to 1. This expansion makes traditional identity and access management frameworks insufficient on their own. At OAD Technologies, we view this shift as an opportunity to architect more resilient, automated systems that protect every digital interaction. The average cost of a data breach in the Middle East reached AED 29.6 million in 2023, making the stakes for modernizing your architecture higher than ever.
The threat environment is evolving just as quickly. AI-driven attacks, including sophisticated deepfakes, are targeting regional financial hubs. A 2024 report indicated that 75% of security professionals in the GCC expect AI-enhanced social engineering to be their primary concern. To counter this, OAD Technologies integrates real-time anomaly detection. Our platform identifies subtle deviations in access patterns, ensuring your infrastructure remains secure against synthetic identities. We don’t just react to threats; we anticipate them through predictive modeling. For a comprehensive overview of IAM and its foundational pillars, it’s helpful to look at how these core concepts are being adapted for a machine-first world. This evolution aligns with the UAE’s National Cybersecurity Strategy, which emphasizes the protection of critical digital assets through advanced technology.
Securing the Non-Human Workforce
Machine identities—such as service accounts, APIs, and the IoT devices used in modern business automation solutions from specialists like Rocatech—frequently possess elevated privileges that exceed those of senior executives. They don’t have working hours, fixed physical locations, or biometric signatures, making them difficult to monitor using legacy tools. We’ve found that 60% of these identities are over-privileged, often retaining access to sensitive databases long after their specific task is complete. To manage this risk, OAD Technologies implements a tailored Machine Identity Management strategy. We start by discovering every active non-human account across your hybrid cloud environment. Next, we apply Cloud Security Posture Management (CSPM) to catch identity-based misconfigurations. This proactive approach reduces the risk of a single leaked API key leading to a breach that could cost your firm millions of dirhams in regulatory fines and lost trust.
- Automated Lifecycle Management: We ensure machine credentials are rotated every 24 hours to minimize the window of exploitation.
- Least Privilege Enforcement: Our architects strip away unnecessary permissions, ensuring bots only access the specific data required for their function.
- CSPM Integration: We use CSPM tools to provide a 360-degree view of your cloud, flagging any identity that bypasses established security protocols.
AI and Behavioral Analytics
The era of “Point-in-Time” authentication is ending. Validating a user or machine only at the moment of login leaves a massive window of vulnerability if a session is hijacked later. We’re leading the transition toward Continuous Authentication. Our systems use machine learning to calculate a dynamic risk score for every active session. If a user’s behavior shifts suddenly, the system triggers a re-authentication challenge or terminates the connection immediately. This behavioral analysis tracks 50 unique data points, from typing cadence and mouse movements to access times and geographic velocity. It’s a bespoke approach that turns identity and access management into a living, reactive shield. By focusing on how users actually behave rather than just the credentials they hold, we provide a level of security that is both invisible to the user and impenetrable to the attacker.
Implementing a Zero Trust IAM Strategy: A Step-by-Step Roadmap
Most UAE enterprises operate within a fragmented ecosystem where legacy on-premise systems clash with modern cloud environments. This fragmentation creates identity silos that obscure visibility and increase the attack surface. We’ve observed that 60% of regional security breaches originate from compromised credentials. Transitioning to a unified identity fabric isn’t just a technical upgrade; it’s a strategic shift toward a Zero Trust model where no entity is trusted by default. This process begins with a rigorous technical assessment and Vulnerability Assessment and Penetration Testing (VAPT). VAPT is critical because it uncovers misconfigured permissions and hidden backdoors that automated tools often miss. By identifying these weaknesses early, we ensure your identity and access management framework is built on a resilient foundation rather than a compromised one.
Step 1: Inventory and Discovery
Security starts with visibility. You can’t protect what you don’t know exists. We begin by cataloging every human user, service account, and machine identity across your entire network. This phase is vital for uncovering “Shadow IT,” which accounts for roughly 35% of cloud service usage in Dubai’s fast-paced business sectors. We also prioritize the removal of orphan accounts; those belonging to former employees or expired contractors. These accounts are prime targets for lateral movement during a breach. A clean inventory ensures your identity and access management system only manages active, authorized entities.
Step 2: Define and Enforce Least Privilege
Granular control is the heart of Zero Trust. We map every identity to specific business functions using Role-Based Access Control (RBAC). Instead of granting broad administrative rights, we provide users with the minimum level of access required to complete their tasks. This strategy significantly reduces the “blast radius” of a potential incident. If one account is compromised, the attacker’s movement is restricted to that specific role’s permissions. In the context of UAE NESA compliance, enforcing least privilege is a mandatory step for securing critical information infrastructure. It transforms your security posture from reactive to proactive.
Step 3: Deploy Adaptive MFA and SSO
The final step involves balancing high security with user experience. We implement Single Sign-On (SSO) combined with Adaptive Multi-Factor Authentication (MFA). Adaptive MFA uses contextual signals like geolocation, device health, and time of day to trigger additional verification only when a login attempt looks suspicious. This reduces friction for employees while maintaining a hard barrier against threats. There’s a clear financial incentive here too. The average cost of a manual password reset in the UAE is approximately AED 70 per helpdesk ticket. By automating these processes through a unified portal, organizations often see a 40% reduction in helpdesk volume within the first six months. This efficiency allows your IT team to focus on strategic growth rather than routine maintenance.
Scalability is the ultimate goal of this roadmap. We don’t just solve for your current headcount; we build a bespoke architecture that grows with your digital transformation. This future-proof approach ensures that as you adopt new AI tools or expand into new markets, your security framework remains agile. If you are ready to secure your infrastructure with a tailored solution, partner with OAD Technologies to architect your Zero Trust future.
Bespoke IAM Solutions: Why OAD Technologies is Your Expert Architect
OAD Technologies doesn’t operate as a simple software vendor. We act as your strategic partner and expert architect. We recognize that identity and access management serves as the primary defense line for modern UAE enterprises. Generic, off-the-shelf solutions often fail because they don’t account for unique operational workflows or regional compliance mandates like the NESA (National Electronic Security Authority) standards or Dubai’s ISR (Information Security Regulation). We build bespoke frameworks that align with your specific risk profile and business objectives.
Our methodology integrates identity protocols directly with your broader security stack. By linking identity and access management with Endpoint Detection and Response (EDR) and Security Information and Event Management (SIEM), we create a unified ecosystem. This holistic posture is critical. IBM’s 2024 Cost of a Data Breach Report highlights that stolen credentials remain the most common initial attack vector. In the Middle East, the average cost of a data breach has climbed to over 30 million AED. We mitigate this financial risk by ensuring every access point is monitored and every identity is verified through rigorous, context-aware policies.
We pride ourselves on bridging the gap between high-level innovation and practical business results. Our team focuses on the intersection of human intelligence and machine capability, ensuring technology empowers your employees rather than creating friction. This approach delivers several key benefits for your organization:
- Regulatory Alignment: We ensure your systems meet the strict data residency and privacy requirements of the UAE.
- Operational Efficiency: Automated provisioning and de-provisioning reduce the workload on your IT staff.
- Reduced Attack Surface: Implementing Zero Trust principles ensures that users only have the minimum access necessary for their roles.
- Scalability: Our architectures grow with your business, whether you’re expanding in Abu Dhabi or going global.
Tailored Integration and Managed Monitoring
We begin every partnership with a professional technical assessment. This isn’t a surface-level scan; it’s a deep dive into your existing infrastructure to identify hidden vulnerabilities. Once deployed, our UAE-based Security Operations Center (SOC) provides 24/7 managed monitoring. We track identity and access management events in real-time, detecting anomalies like impossible travel or brute-force attempts before they escalate into full-scale incidents. This proactive oversight ensures your system remains an active shield rather than a passive gate.
Future-Proofing Your Enterprise
Cyber threats evolve rapidly. What worked in 2023 won’t stop the AI-driven phishing attacks of 2025. OAD Technologies commits to keeping your organization resilient through continuous optimization and adaptive security controls. We empower your team with high-level innovation that delivers measurable ROI. Don’t leave your perimeter to chance. You can Schedule a Strategic IAM Assessment with OAD Technologies to secure your digital future and ensure long-term relevance in an ever-changing market.
Future-Proof Your Security Architecture Today
By 2026, the traditional network perimeter will be entirely replaced by identity-centric security. Organizations in the UAE must adapt to this shift by prioritizing Zero Trust frameworks that comply with NESA and DESC standards. Managing the surge in machine identities and AI-driven access points is now critical for maintaining operational continuity. A robust identity and access management strategy isn’t just a technical requirement; it’s a strategic asset that protects your business growth across the GCC.
OAD Technologies serves as your expert architect in this transition. Our Dubai-based team brings deep knowledge of local regulatory landscapes and specializes in integrating multi-cloud CSPM with bespoke IAM solutions. Our industry-leading security engineers don’t offer generic templates. We build tailored systems designed for high-level performance and long-term resilience. You’ll gain a clear roadmap that bridges the gap between complex innovation and practical business results.
Secure Your Identity Perimeter with an OAD Strategic Assessment
Your journey toward a more secure and scalable digital future starts with a single, decisive step. We’re ready to help you lead the way.
Frequently Asked Questions
What is the difference between IAM and IGA?
IAM focuses on the operational mechanics of access, while Identity Governance and Administration (IGA) manages the policy and compliance layer. IAM provides the tools for daily logins and session management. IGA adds a layer of oversight to ensure users only have access they’re authorized to hold. By 2025, 70% of organizations will converge these functions to eliminate security gaps between administration and governance.
How does IAM support compliance with the UAE Personal Data Protection Law (PDPL)?
Identity and access management supports UAE PDPL compliance by enforcing strict data sovereignty and the principle of least privilege. Since the Law took effect in January 2022, companies must prove they’ve secured personal data against unauthorized access. IAM systems provide the granular audit trails required for Article 13 compliance. Automating user de-provisioning reduces the risk of data leaks by 40% when employees exit the firm.
Can IAM prevent ransomware attacks?
IAM acts as a critical barrier against ransomware by stopping lateral movement within your network. Most ransomware variants rely on stolen credentials to escalate privileges across systems. Implementing Privileged Access Management (PAM) blocks 80% of these security breaches. By requiring step-up authentication for access to sensitive databases, IAM ensures that a single compromised account doesn’t lead to a total system lockout or data encryption.
What are machine identities and why do they need management?
Machine identities include non-human entities like APIs, workloads, and bots that require credentials to function. These identities now outnumber human users by a ratio of 45 to 1 in modern cloud environments. Without proper management, these “secret” keys become easy targets for attackers. To enhance security and verifiability, many organizations now leverage a blockchain digital certificate platform to manage the lifecycle of these credentials. OAD Technologies implements automated lifecycle management for these certificates. This process prevents service outages and closes high-risk security gaps in your automated workflows.
Is MFA enough to secure my enterprise identities in 2026?
Standard MFA won’t be sufficient in 2026 because 90% of traditional SMS or push-based codes are now vulnerable to sophisticated phishing kits. Enterprises must transition toward FIDO2-compliant, passwordless authentication. This shift removes the human element from the security chain. By 2026, we expect 75% of UAE enterprises to adopt phishing-resistant MFA as their baseline. Relying on legacy methods leaves a 30% gap that AI-driven attacks will exploit.
How long does a typical IAM implementation take for a medium-sized enterprise?
A typical IAM implementation for a medium-sized enterprise in Dubai or Abu Dhabi takes between 4 and 9 months. The initial discovery and architecture phase usually spans 6 weeks. Following this, core deployment and integration with existing HR systems takes another 12 to 16 weeks. Professional service costs for these projects often range from AED 150,000 to AED 450,000. A phased rollout ensures your daily operations continue without interruption.
What is the role of AI in modern Identity and Access Management?
AI transforms modern identity and access management by introducing behavioral analytics to detect threats in real time. Instead of relying on static rules, AI monitors 50 or more variables like login patterns and device health. If a user accesses sensitive files at 3:00 AM from a new IP, the system triggers an automatic lockout. This proactive approach reduces the time to detect an identity breach by 60% compared to manual monitoring.
How does OAD Technologies customize IAM for different industry sectors?
OAD Technologies rejects one-size-fits-all software in favor of bespoke blueprints that address specific regulatory demands. For UAE’s financial services, we prioritize high-assurance authentication and transaction signing. For healthcare providers, we focus on HIPAA-aligned access controls for patient records. Our architects ensure every solution scales with your 5-year growth plan. This tailored approach provides a clear ROI and future-proofs your digital infrastructure against evolving regional threats.


