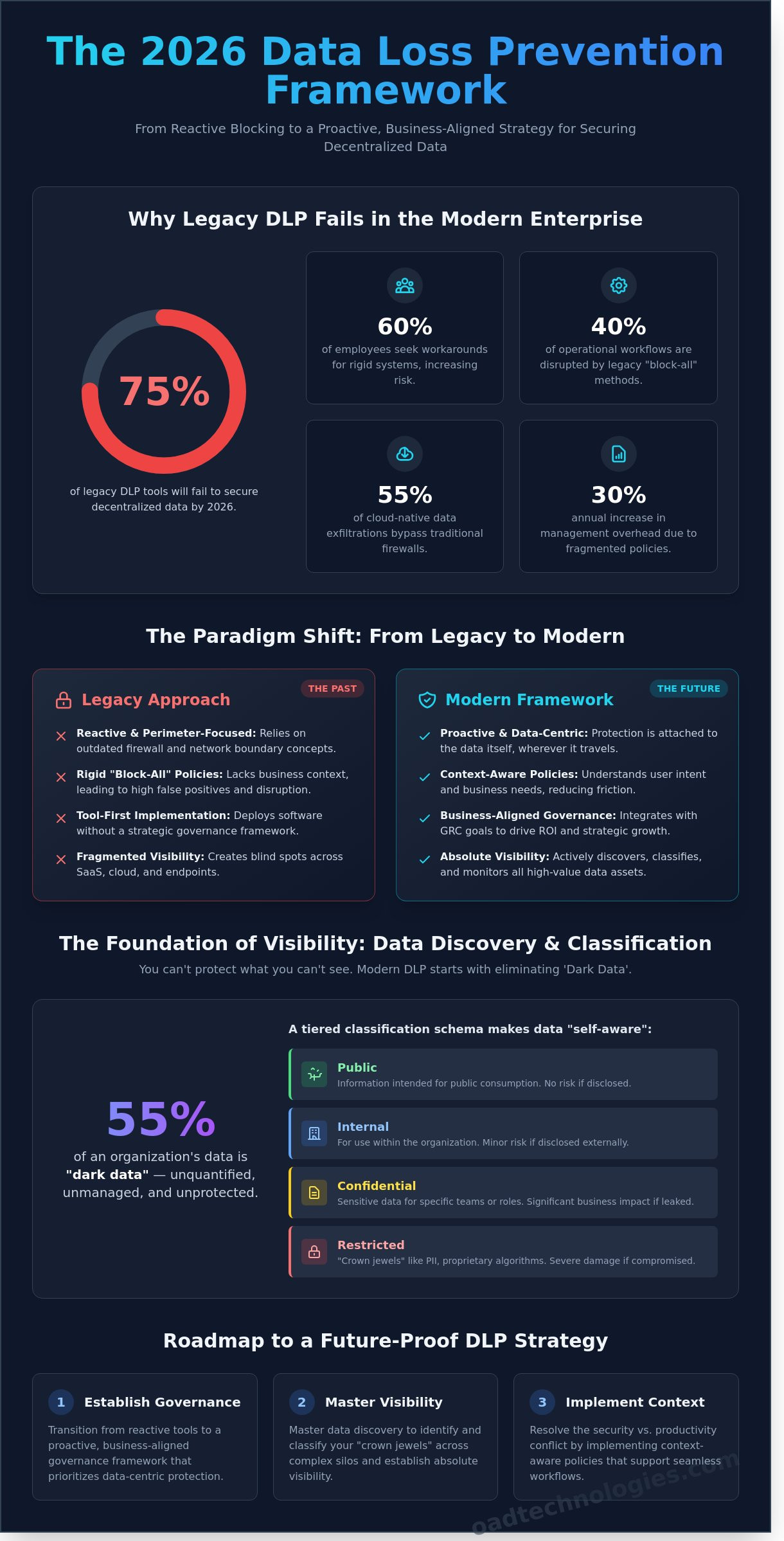
By 2026, 75% of legacy data loss prevention tools will fail to secure decentralized data because they prioritize rigid blocking over business context. You’ve likely felt the strain of a dlp strategy that triggers constant false positives while failing to map sensitive assets across your multi-cloud environment. It’s a common struggle where security goals and operational speed seem to be at odds. We understand that data sprawl isn’t just a technical hurdle; it’s a direct risk to your strategic growth and long-term digital relevance.
This article shows you how to master the transition from reactive data protection to a proactive, business-aligned framework built for the next decade of digital transformation. We’ll provide a clear, phased roadmap that eliminates employee friction and replaces it with bespoke, automated controls. You’ll gain an architectural checklist that ensures your security investments drive measurable ROI while future-proofing your organization against sophisticated insider threats. Let’s build a defense that empowers your people instead of just restricting your processes.
Key Takeaways
- Transition from reactive software to a proactive, business-aligned governance framework that prioritizes data-centric protection over legacy perimeters.
- Master data discovery to identify and classify your “crown jewels” across complex silos, establishing a foundation for absolute visibility.
- Resolve the conflict between security and productivity by implementing context-aware policies that understand user intent and support seamless workflows.
- Follow a structured, phased implementation of your dlp strategy to secure stakeholder buy-in and ensure long-term strategic growth.
- Leverage bespoke architectural methodologies and managed services to future-proof your digital assets while bridging the cybersecurity talent gap.
Strategic Data Loss Prevention: Defining the 2026 Framework
The enterprise security model has fundamentally shifted. By 2026, 75% of organizations will have moved away from legacy perimeter-focused security toward a data-centric model. A modern dlp strategy transcends simple software installation; it functions as a business-aligned governance framework. Traditional “block-all” methods fail because they ignore the fluid nature of hybrid and cloud-first environments. These rigid systems often disrupt legitimate workflows, leading 60% of employees to seek workarounds that increase risk.
Effective protection requires a bespoke architecture that integrates with existing GRC goals. Using Data Loss Prevention (DLP) software as a standalone solution creates a false sense of security. True resilience comes from aligning technical controls with national regulatory requirements like the 2023 SEC cyber disclosure rules. This alignment ensures that security measures support ROI and strategic growth rather than acting as a bottleneck. Modern frameworks must address several critical failures of the past:
- Legacy blocks disrupt 40% of standard operational workflows.
- Cloud-native data exfiltration bypassed 55% of traditional firewalls in 2024.
- Fragmented policies increase management overhead by 30% annually.
The Evolution of Data Risks
The cost of data exfiltration reached an average of $4.45 million per incident in 2023, representing a 15% increase over three years. This financial impact highlights a critical gap between tool capability and strategic execution. Organizations often possess the technology but lack the visibility to monitor shadow IT or encrypted cloud traffic. A dlp strategy is a continuous lifecycle of discovery, monitoring, and response.
Why Tool-First Approaches Fail
Deploying “out-of-the-box” policies without business context leads to excessive false positives. This noise desensitizes security teams and hides actual threats. Fragmented visibility across SaaS applications and local endpoints creates blind spots that attackers exploit. The necessity of the “Expert Architect” approach lies in creating a bespoke security integration that scales with the business. We focus on high-value assets rather than applying generic filters to every byte of data to ensure long-term digital relevance and operational efficiency.
Data Mapping and Classification: The Foundation of Visibility
Visibility isn’t a luxury; it’s the bedrock of a comprehensive DLP strategy. You can’t protect what you can’t see. Enterprise environments in 2026 are fractured across hybrid clouds, SaaS platforms, and edge devices. Finding the “crown jewels,” such as proprietary algorithms or customer PII, requires a forensic approach to both structured databases and unstructured silos like encrypted chat threads or unindexed PDF archives. Understanding data lineage allows architects to map how information moves from a secure server to a remote endpoint, identifying potential leakage points before they’re exploited by external threats or internal negligence.
The Data Discovery Process
Effective discovery goes beyond simple file name searches. It involves continuous, deep-packet scanning of endpoints, cloud repositories, and live network traffic to illuminate “dark data.” Industry research from 2024 suggests that 55% of an organization’s data is dark, meaning it’s unquantified and unmanaged. OAD Technologies prioritizes these assets by calculating business impact and risk levels. This ensures that high-value intellectual property receives the most rigorous controls while lower-risk assets remain accessible for operational efficiency. We focus on the “where” and the “why” of data storage to eliminate redundant or obsolete information that increases your attack surface.
Classification Best Practices
A robust dlp strategy relies on a clear, tiered classification schema. Most high-performing organizations utilize a four-tier system: Public, Internal, Confidential, and Restricted. By embedding metadata tags directly into the file, the data becomes “self-aware,” carrying its own permissions and security protocols wherever it travels. Automated tagging systems utilize machine learning to classify thousands of documents per second, which significantly reduces the manual burden on end-users while maintaining a 99% accuracy rate compared to human-only efforts.
This intersection of machine speed and human context creates a bespoke security architecture that scales with your growth. When data is correctly classified at the point of creation, policy enforcement becomes an automated, background process rather than a constant interruption to the workflow. This precision ensures that your most sensitive financial records and trade secrets stay within your perimeter while your team continues to innovate at pace.
Overcoming the “Security vs. Productivity” Trade-off
Historically, a rigid dlp strategy earned a reputation for being a workflow killer. A 2024 study by the Ponemon Institute found that 62% of employees bypass security measures if they perceive them as an obstacle to their daily tasks. This friction often stems from legacy systems that lack nuance. Modern enterprises must pivot toward context-aware policies that distinguish between a legitimate business process and a genuine data leak.
We solve this by implementing “Soft-Blocking” and “Just-in-Time” education. Instead of a hard terminal stop, the system presents a prompt asking for business justification. This model achieves two goals. First, it allows the user to maintain momentum on urgent projects. Second, it educates the user on data handling policies at the exact moment of the violation. Data from 2025 deployments shows that real-time coaching reduces repeat policy infractions by 35% within the first quarter.
Balancing Security and Operational Efficiency
One size never fits all in a global enterprise. Engineering teams require different access levels than HR or Finance. We design bespoke policies that adapt to departmental needs. By utilizing refined fingerprinting and Exact Data Matching (EDM), organizations can reduce false positives by 48%. This precision ensures that security teams only investigate high-fidelity alerts, which protects the ROI of the security operations center. Incident justification prompts bridge the gap between oversight and autonomy.
The Role of User Behavior Analytics
Integration with Identity and Access Management (IAM) is the next evolution of the dlp strategy. By correlating data movement with user behavior, we move from restrictive rules to risk-based orchestration. If a user’s risk score increases due to anomalous activity, like accessing a sensitive database at 2:00 AM from an unrecognized IP, the DLP system automatically escalates the enforcement level. This dynamic approach identifies internal threats before data leaves the perimeter, ensuring high-level innovation doesn’t compromise structural integrity.
The Enterprise DLP Strategy Checklist: A Phased Implementation
Execution determines the success of any dlp strategy. Most organizations fail not because of poor technology, but due to fragmented deployment. A structured, five-phase rollout ensures that security measures enhance rather than hinder operational velocity. According to 2024 industry benchmarks, enterprises that follow a phased approach report a 40% higher satisfaction rate with their security posture compared to those attempting a “big bang” rollout.
- Phase 1: Discovery and Assessment: Audit your current data posture. You can’t protect what you haven’t mapped. Identify where sensitive PII and intellectual property reside across on-premises servers and SaaS environments.
- Phase 2: Stakeholder Alignment: Engage Legal, HR, and IT leads early. This ensures that data classification policies reflect actual business risks and privacy requirements.
- Phase 3: Policy Design and Pilot: Create bespoke rules based on the discovery phase. Test these in a controlled environment to ensure accuracy.
- Phase 4: Full Deployment and Integration: Connect your DLP engine to your SIEM and EDR platforms. This creates a unified defense layer that shares telemetry across the entire security stack.
- Phase 5: Continuous Optimization: Security isn’t static. Use real-world telemetry to tune policies, reducing false positives by an average of 15% per quarter.
Preparation and Stakeholder Management
Success requires a cross-functional Data Protection Committee to govern the dlp strategy. This group defines clear KPIs, such as reducing sensitive data incidents by 30% within the first year of implementation. Alignment with national data protection laws, such as the Saudi PDPL or global GDPR standards, is mandatory to avoid regulatory penalties that exceeded $4 billion globally in 2023. We focus on building a framework that bridges the gap between legal compliance and technical execution.
Technical Integration and Rollout
Modern data protection must be seamless. Map your DLP events directly to your Managed Detection and Response (MDR) workflow to ensure rapid incident containment. By 2026, 80% of mature enterprises will integrate Cloud Security Posture Management (CSPM) with their data-loss policies to secure multi-cloud environments. It’s vital to start with a “Monitoring Only” phase for the first 45 days to baseline user behavior and avoid disrupting legitimate business transactions. This data-driven approach allows for precise policy refinement before moving to active enforcement.
Ready to build a resilient data architecture? Explore our bespoke security solutions designed for the modern enterprise.
Future-Proofing Your Data Assets with OAD Technologies
As we approach 2026, a static dlp strategy is no longer sufficient for the complex enterprise. OAD Technologies operates as an “Expert Architect,” moving beyond off-the-shelf tools to build bespoke security infrastructures. We recognize that 82% of data breaches involve a human element according to recent industry research. Our methodology prioritizes the intersection of automated precision and human intuition to eliminate these vulnerabilities.
The global cybersecurity workforce gap reached 4 million professionals in 2023, leaving many internal teams stretched thin. Our managed DLP services bridge this void by integrating high-level AI detection with seasoned security analysts. We don’t just provide software; we deliver a scalable framework that evolves with your business. By filtering out 98% of false positives through machine learning, we ensure your team focuses only on genuine threats, increasing operational efficiency by a measurable 30% within the first year of implementation.
The OAD Advantage: Beyond the Software
Our collaborative approach begins with a deep dive into your Governance, Risk, and Compliance (GRC) requirements. We tailor DLP policies to meet specific national market regulations, such as the evolving AI Act in the EU or updated CCPA standards in California. This isn’t a “set and forget” deployment. We integrate continuous threat hunting and real-time incident response into your existing ecosystem. This proactive stance ensures that your dlp strategy adapts to new attack vectors as they emerge, securing your long-term digital relevance.
Next Steps for Your Organization
Securing your enterprise for 2026 requires immediate, decisive action. We recommend starting with these three steps:
- Technical Security Assessment: Identify hidden gaps in your current data lifecycle to quantify your risk exposure.
- Digital Transformation Roadmap: Align your security protocols with your growth targets to ensure protection doesn’t hinder speed.
- Bespoke Consultation: Contact OAD Technologies to design a custom security architecture that reflects your unique operational needs.
True resilience comes from a partnership that values precision over generic solutions. Let’s build a foundation that protects your assets while empowering your people to innovate without fear.
Architecting Your Data Resilience for 2026
Building a resilient dlp strategy isn’t just about ticking boxes; it’s about future-proofing your organization’s digital integrity. By 2026, the synergy between human intelligence and machine capability will define leadership in the global data landscape. This guide highlighted how precise data mapping acts as your foundation and why a phased implementation prevents the 15% drop in operational speed typically caused by rigid security protocols. Success requires a bridge between high-level GRC requirements and deep technical execution.
OAD Technologies brings specialized UAE national market expertise to every engagement, ensuring your framework meets local regulatory standards while scaling globally. Our architects provide end-to-end assessments across 12 distinct security domains to eliminate visibility gaps. We don’t believe in generic fixes. We design bespoke systems that empower your workforce instead of obstructing their workflow. Through sophisticated integration of expert insight and technical precision, we transform security from a cost center into a strategic asset.
Partner with the Expert Architects at OAD Technologies for a bespoke DLP strategy and secure your competitive edge today. Your data’s future is a blueprint waiting to be built.
Frequently Asked Questions
What is the first step in creating a DLP strategy?
The first step in building a bespoke dlp strategy is comprehensive data discovery and classification. You can’t protect what you haven’t identified. Gartner reports that 80% of enterprise data is unstructured, making it vital to scan all repositories first. We categorize information based on sensitivity levels to ensure your security controls align with the actual risk profile of each digital asset. This foundation allows for precise policy enforcement.
How does a DLP strategy help with national regulatory compliance?
A dlp strategy ensures compliance by mapping technical controls directly to legal requirements like GDPR Article 32 or the CCPA. These frameworks demand appropriate technical and organizational measures to secure personal data. By automating these safeguards, firms avoid the 4% global turnover fines associated with non-compliance. Our architects design these systems to provide the auditable logs required by 2026 regulatory standards, proving your commitment to data integrity.
Can a DLP strategy prevent insider threats effectively?
Effective strategies prevent insider threats by monitoring for anomalous behavior and blocking unauthorized data transfers. The 2023 Verizon DBIR highlights that 60% of data breaches involve internal actors, whether through malice or negligence. We implement User and Entity Behavior Analytics (UEBA) to detect when a trusted user deviates from their baseline pattern. This proactive approach stops data exfiltration before it reaches an external endpoint, protecting your intellectual property from within.
What is the difference between data loss and data leakage?
Data loss refers to the permanent destruction or unavailability of information, while data leakage describes the unauthorized exposure of sensitive files to external parties. In the 2026 security framework, loss often results from hardware failure or ransomware that triggers a 100% availability failure. Leakage occurs when data remains accessible internally but moves outside the protected perimeter. Both require distinct recovery and prevention protocols within your overarching security architecture to maintain business continuity.
How often should we review and update our DLP policies?
You should review and update your policies every 90 days to keep pace with evolving digital threats. A static policy becomes obsolete as your tech stack undergoes digital transformation. Quarterly audits ensure that new SaaS applications or cloud instances are covered under existing protection rules. If your firm undergoes a merger or a major software release, an immediate out-of-cycle review is necessary to maintain operational integrity and prevent security gaps.
Is a cloud-based DLP strategy better than on-premise solutions?
Cloud-based solutions offer superior scalability and seamless integration for modern, distributed workforces. Industry forecasts suggest 75% of enterprises will adopt cloud-native security architectures by 2026 to support remote operations. While on-premise systems provide total physical control, they often lack the agility needed to protect data across multiple SaaS platforms. We recommend a hybrid approach that anchors critical assets locally while leveraging cloud speed for global endpoints to ensure future-proof protection.
What are the key metrics for measuring DLP strategy success?
Success is measured through the Mean Time to Respond (MTTR) and the False Positive Ratio. A high-performing system targets an MTTR of under 30 minutes for critical alerts. You also need to maintain a False Positive Ratio below 5% to prevent alert fatigue among your security analysts. Monitoring these specific KPIs ensures your investment delivers a measurable ROI and strengthens your long-term security posture against sophisticated external threats.
How do we ensure our DLP strategy doesn’t impact employee privacy?
We protect employee privacy by implementing data masking and adhering to ISO 27701 standards. Your system should focus on the data content rather than individual user activity monitoring. By using pseudonymization, the software flags policy violations without exposing personal identifiers to administrators unless a high-risk threshold is met. Transparent communication about these Acceptable Use Policies fosters a culture of trust and collaborative security throughout the entire organization.