By the end of 2025, the average cost of a data breach in the Middle East is projected to climb past 30.2 million AED. This figure isn’t just a statistic; it’s a wake-up call for UAE organizations relying on fragmented systems that don’t communicate. You’ve likely seen how a lack of cohesion between tools creates blind spots, making it nearly impossible to maintain a 24/7 defense without an army of in-house experts. Deploying effective enterprise cybersecurity solutions in this environment requires a shift from reactive patching to a bespoke, architected defense that treats security as a driver of operational efficiency.
You’re right to feel that the growing complexity of NESA and Dubai ISR regulations requires a more sophisticated approach than a standard off-the-shelf product can provide. We’ll show you how to integrate Data Loss Prevention, Managed Detection and Response, and GRC into a unified framework designed for the 2026 threat landscape. This article previews a strategic roadmap to help you achieve a 40 percent reduction in Mean Time to Respond while ensuring your compliance is always audit-ready.
Key Takeaways
- Understand the critical transition from perimeter-based security to a 2026-ready architecture centered on data-centric and identity-centric protection models.
- Master the integration of advanced enterprise cybersecurity solutions like DLP and MDR to safeguard your organization’s most valuable assets with 24/7 expert vigilance.
- Learn to eliminate dangerous blind spots by orchestrating a unified security stack that centralizes telemetry for actionable, high-level strategic insights.
- Navigate the complexities of the UAE regulatory landscape, ensuring full alignment with the Personal Data Protection Law (PDPL) and Information Security Regulation (ISR).
- Discover how a bespoke security philosophy bridges the gap between sophisticated engineering and practical ROI to future-proof your digital transformation.
The Evolution of Enterprise Cybersecurity Solutions in 2026
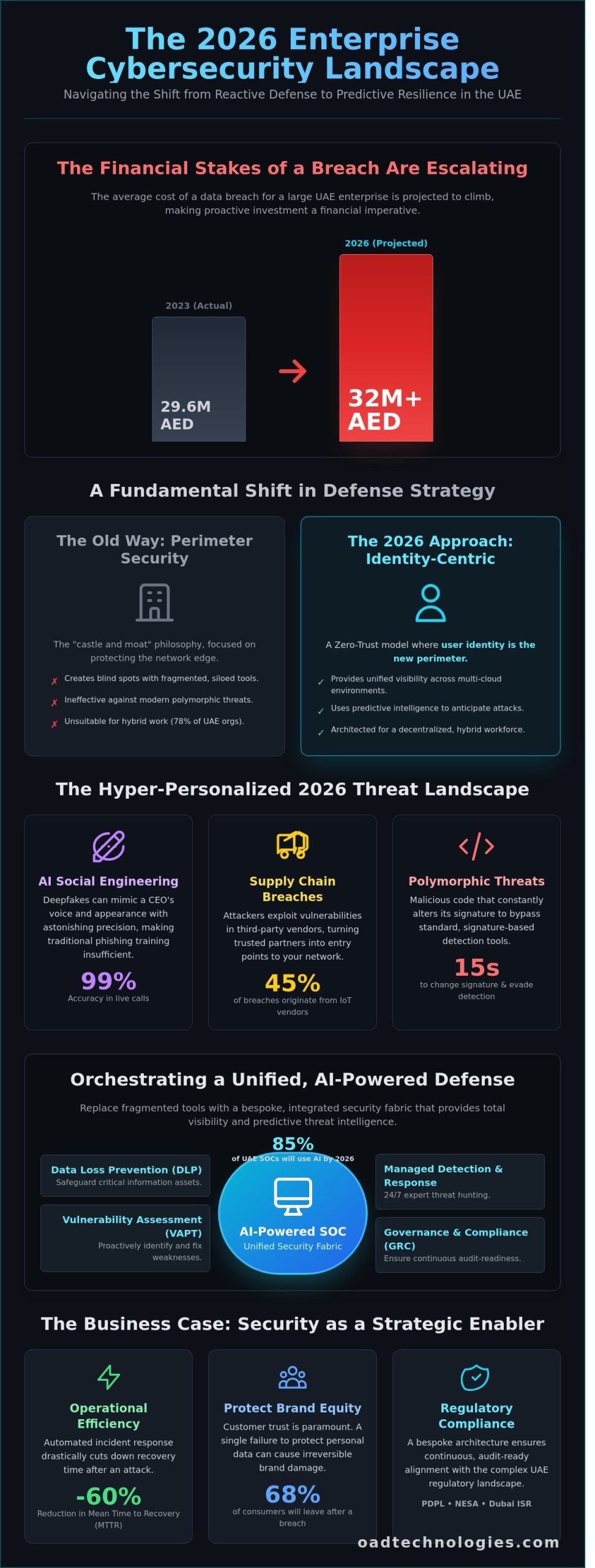
Enterprise security no longer functions as a single barrier at the edge of a network. It has transformed into a complex, fluid ecosystem designed to protect data wherever it lives. Modern enterprise cybersecurity solutions have shifted away from the traditional “castle and moat” philosophy toward an identity-centric model. This change is mandatory in the UAE, where 78% of organizations now operate under hybrid work structures. We’ve moved into an era where the user identity is the new perimeter. Every access request is verified regardless of its origin, reflecting a zero-trust maturity that was aspirational only a few years ago.
Legacy point solutions, which often operate in isolated silos, are failing to stop modern polymorphic threats. These malicious codes can alter their signature every 15 seconds to bypass standard detection. Relying on a patchwork of disconnected tools creates visibility gaps that attackers exploit with precision. This shift in defense strategy aligns with core cybersecurity principles of confidentiality and integrity, but applies them through a decentralized, cloud-native lens. OAD Technologies approaches this challenge as an expert architect, replacing fragmented tools with a unified, bespoke fabric that provides total visibility across multi-cloud environments.
Artificial intelligence and machine learning serve as the backbone of this 2026 defense strategy. We don’t just react to alerts; we use predictive threat intelligence to anticipate attacks before they manifest. By 2026, 85% of UAE security operations centers will utilize AI to automate the initial stages of threat hunting. This human-machine collaboration allows security teams to focus on high-level strategy while the system neutralizes thousands of low-level anomalies every hour.
The 2026 Threat Landscape: Beyond Ransomware
Threats have become hyper-personalized. AI-driven social engineering now utilizes deepfakes that can mimic a CEO’s voice or appearance with 99% accuracy during live video calls. This has made traditional phishing training insufficient. Supply chains have also become a primary target. In late 2025, 45% of UAE organizations reported a breach that originated from a third-party IoT vendor. Moving from a “detect and respond” mindset to “predict and prevent” is the only way to secure these hyper-connected ecosystems. It’s about building a resilient infrastructure that expects the attempt but denies the execution.
The Business Case for Advanced Security Architecture
The financial argument for robust enterprise cybersecurity solutions is undeniable. By 2026, the average cost of a data breach for a large UAE enterprise is projected to exceed 32 million AED. This includes regulatory fines under the UAE Data Protection Law and the catastrophic loss of operational uptime. Investing in prevention offers a clear ROI by significantly lowering cyber-insurance premiums and protecting brand equity. In our local market, 68% of consumers state they’ll immediately stop doing business with a brand that fails to protect their personal data. Security is no longer a cost center; it’s a strategic enabler that allows businesses to innovate and scale with confidence.
- Strategic Growth: Secure systems allow for faster adoption of emerging technologies.
- Operational Efficiency: Automated incident response reduces the mean time to recovery (MTTR) by 60%.
- Regulatory Compliance: Bespoke architectures ensure continuous alignment with the Dubai Cyber Security Strategy 2.0.
Core Pillars of a Resilient Enterprise Protection Framework
Modern enterprise cybersecurity solutions must move beyond simple perimeter firewalls to address a decentralized workforce. In the UAE, where the average cost of a data breach reached AED 29.6 million in 2023 according to IBM reports, the financial stakes of a security failure are immense. A robust architecture aligns with the NIST Cybersecurity Framework to ensure every digital touchpoint remains fortified against sophisticated threat actors. This strategy focuses on building layers of defense that protect data, identities, and endpoints with equal rigor.
Data Loss Prevention (DLP) and Information Integrity
Data serves as the lifeblood of the modern corporation, making its protection a non-negotiable priority. Effective DLP strategies distinguish between three critical states: data at rest within local servers, data in motion across networks, and data in use at the endpoint level. Each state requires specific encryption and monitoring protocols to prevent unauthorized exfiltration.
Implementing bespoke DLP policies ensures that security measures don’t hinder daily productivity. For instance, a financial firm in Dubai might restrict the transfer of sensitive IBAN details to external drives while allowing seamless internal collaboration. These policies must also account for UAE Federal Decree Law No. 45 of 2021 regarding the Protection of Personal Data. This regulatory landscape demands strict data sovereignty, ensuring that sensitive information remains within national borders unless specific legal exemptions apply. By automating these controls, businesses can maintain compliance without manual oversight. If you’re looking to upgrade your compliance posture, exploring a bespoke security architecture can provide the necessary technical foundation.
MDR and EDR: The Frontline of Real-Time Defense
While automated tools catch 90% of common threats, the remaining 10% represent targeted, sophisticated attacks that require human intervention. Endpoint Detection and Response (EDR) monitors individual devices for suspicious behavior, providing the granular visibility needed to isolate infected laptops or servers before a breach spreads. However, EDR is only as effective as the team monitoring the alerts.
- Expert Oversight: Managed Detection and Response (MDR) provides 24/7 vigilance through expert Security Operations Centers (SOCs) that interpret complex telemetry.
- XDR Evolution: The industry is shifting toward Extended Detection and Response (XDR), which integrates data from email, cloud, and network layers to provide a holistic view of the attack surface.
- Proactive Partnership: Managed Detection and Response represents a proactive partnership for 2026 where human intelligence and predictive analytics converge to neutralize threats before they impact the bottom line.
Identity and Access Management (IAM): The New Perimeter
As 74% of UAE organizations embrace hybrid work models, the traditional office boundary has vanished. Identity is the new perimeter. IAM systems ensure that only the right individuals have access to specific resources at the right time. This involves more than just strong passwords; it requires Multi-Factor Authentication (MFA) and Zero Trust architectures where every access request is continuously verified. By implementing role-based access controls, enterprises minimize the “blast radius” of a potential credential compromise, ensuring that a single breached account doesn’t lead to a total system takeover. This structured approach to identity management is a fundamental component of modern enterprise cybersecurity solutions, providing the scalability needed for rapid business growth.
Beyond Tool Sprawl: Orchestrating an Integrated Security Stack
Fragmented security architectures represent a primary vulnerability for UAE enterprises. Recent data indicates that large organizations in Dubai and Abu Dhabi manage an average of 65 discrete security tools. These disconnected systems create the “Silo Problem,” where critical telemetry remains trapped within individual applications. This lack of communication allows sophisticated threats to move laterally across a network undetected. When tools don’t talk to each other, security teams lose the context needed to identify complex attack patterns.
A Security Information and Event Management (SIEM) system serves as the centralized brain of your defense. It ingests vast amounts of data from across your infrastructure to provide actionable insights. By aggregating logs from firewalls, endpoints, and identity providers, the SIEM identifies anomalies that a single tool would miss. This centralized approach is vital for maintaining enterprise cybersecurity solutions that actually protect the bottom line. It transforms raw data into a strategic asset, allowing for faster decision-making during a crisis.
Cloud Security Posture Management (CSPM) is essential as UAE businesses shift to multi-cloud environments. These tools provide continuous visibility into cloud configurations, ensuring compliance with local regulations like the NESA UAE Information Assurance Standards. Effective orchestration requires a NIST Guide to a Secure Enterprise Network Landscape to align internal protocols with global benchmarks. Seamless integration ensures that security doesn’t become a bottleneck for operational continuity. It allows your business to scale without the friction of manual security checks.
Achieving a Unified Security Posture
Modern enterprise cybersecurity solutions rely on API-first architectures to bridge the gap between legacy systems and new cloud native tools. This connectivity allows for intelligent correlation, which drastically reduces alert fatigue by filtering out 85% of false positives. A 2023 OAD Technologies implementation for a Dubai-based logistics firm demonstrated this value clearly. By automating the correlation between endpoint detection and network traffic, the client reduced their incident response times by 60% within the first four months of deployment.
Future-Proofing Your Infrastructure
Scalability is no longer optional. As your data footprint expands, your security stack must grow without requiring massive capital expenditure (CAPEX) in hardware. Adopting Zero Trust Architecture is the foundational principle here. It moves the perimeter from the network edge to the individual user and device. This transition from hardware-heavy appliances to software-defined security allows for more agile responses. It ensures that your digital assets remain protected even as your workforce becomes more distributed across the Emirates and beyond.
Strategic Resilience: VAPT, GRC, and Regulatory Alignment
Resilience isn’t a static state you reach; it’s a discipline you maintain through rigorous engineering and foresight. OAD Technologies operates as an Expert Architect, designing security frameworks that withstand the velocity of modern digital threats. We integrate enterprise cybersecurity solutions that align technical defense with the specific regulatory climate of the UAE, ensuring your infrastructure is both secure and compliant.
Our methodology moves beyond reactive patching. We treat security as a structural requirement, similar to how an architect treats load-bearing walls. By bridging the gap between high-level innovation and practical results, we help organizations transform their security posture from a cost center into a strategic asset. This approach requires a deep understanding of how technical vulnerabilities impact business continuity and long-term growth.
This focus on enabling long-term growth applies across the digital landscape. For an interesting example of a niche agency dedicated to this principle for service contractors, you can visit Door & Gate Domination.
The Necessity of Continuous VAPT
Relying on an annual audit is like checking your pulse once a year to determine your health; it’s insufficient for survival. In 2023, the National Vulnerability Database recorded over 26,000 new security flaws. If your last assessment was six months ago, your defense is already outdated. Continuous Vulnerability Assessment and Penetration Testing (VAPT) ensures that your perimeter evolves as quickly as the threat actors targeting it.
There’s a critical distinction between automated scanning and expert-led penetration testing. While automated tools identify known signatures, they lack the creative intuition of a human adversary. Our experts simulate real-world attacks to uncover complex logic flaws that software misses. We don’t just hand over a list of bugs. We integrate VAPT results into your long-term security roadmap, prioritizing fixes based on their potential impact on your operational efficiency and ROI.
Compliance as a Competitive Advantage
The UAE Personal Data Protection Law (Federal Decree Law No. 45 of 2021) changed the stakes for data sovereignty. Organizations must now meet stringent requirements for data processing and storage. Meeting these standards, along with Dubai ISR and NESA regulations, shouldn’t be viewed as a hurdle. Instead, it’s a signal of maturity that builds trust with international partners and local stakeholders alike.
- Regulatory Precision: We align your systems with GCC-specific standards, including Saudi NCA and Dubai ISR v2.0, to ensure seamless cross-border operations.
- Operational Efficiency: Automating compliance reporting can reduce the administrative burden on your IT team by as much as 35%, allowing them to focus on innovation.
- Strategic Blueprinting: GRC frameworks provide a clear structure for organizational resilience, acting as a guide for scaling your digital footprint safely.
By treating GRC as a blueprint rather than a checklist, you create a foundation for sustainable growth. This structured approach ensures that as your business expands, your security architecture scales with it. We help you move away from fragmented fixes toward a unified strategy that protects your digital relevance in an ever-changing market.
Ready to harden your infrastructure against evolving threats? Consult with our Expert Architects to build a tailored resilience strategy.
Engineering Your Bespoke Security Future with OAD Technologies
OAD Technologies treats cybersecurity as a rigorous engineering discipline rather than a simple product procurement exercise. We believe that enterprise cybersecurity solutions must mirror the unique architectural DNA of your organization to be truly effective. Our philosophy centers on the “Expert Architect” model; we don’t just deploy software; we build resilient digital fortresses designed for longevity. By the start of 2025, an estimated 60% of UAE enterprises will prioritize vendor consolidation to reduce technical debt. OAD bridges this gap by aligning high-level innovation with measurable ROI. We ensure that every dirham spent on your security infrastructure contributes directly to operational uptime and risk mitigation. Our local presence in the UAE means we possess an intimate understanding of the specific regulatory pressures from the National Electronic Security Authority (NESA) and the Dubai Information Security Regulation (ISR). We act as a seamless extension of your internal team, providing the technical depth and 24/7 vigilance that many in-house departments struggle to maintain alone.
Our commitment to precision is reflected in our adherence to global engineering standards. We don’t believe in one-size-fits-all templates because they create blind spots that sophisticated threat actors exploit. Instead, we focus on a collaborative approach that values your long-term success over quick, superficial fixes. This partnership involves a deep dive into your data strategies and software architectures to ensure our enterprise cybersecurity solutions empower your people. We bridge the divide between complex machine capabilities and human intelligence, creating a synergy that enhances decision-making during critical incidents.
The OAD Managed Services Advantage
Accessing elite security capabilities shouldn’t require a massive capital expenditure that drains your annual budget. Our managed services provide direct access to world-class SIEM, EDR, and MDR platforms without the traditional overhead of building a 24/7 Security Operations Center. We specialize in bespoke implementations of Identity and Access Management (IAM) and Cloud Security Posture Management (CSPM) specifically for the UAE market. While a standard SOC setup can cost upwards of AED 1,200,000 in initial hardware and talent acquisition, OAD’s model delivers superior protection at a fraction of that cost. Our clients work directly with senior technical architects and GRC consultants who understand that compliance is a continuous process, not a checkbox.
Next Steps: Securing Your Digital Legacy
The path to a hardened security posture begins with a clear, data-driven baseline. We recommend starting with a comprehensive security maturity assessment to identify hidden vulnerabilities in your current defense layers. Following this audit, OAD builds a phased roadmap for infrastructure protection that prioritizes your most critical assets. This structured approach ensures that your digital transformation remains secure at every milestone. Consider these immediate actions:
- Schedule a technical deep-dive to evaluate your current cloud configuration against UAE-specific standards.
- Review your incident response playbooks to ensure they account for the latest AI-driven threat vectors identified in 2024.
- Contact OAD Technologies for a strategic consultation to align your security spend with your 2025 growth targets.
We’re ready to help you engineer a future where security is a powerful business enabler. By choosing OAD, you’re not just buying a service; you’re securing a partner dedicated to your long-term digital relevance in an increasingly volatile market. Let’s build a roadmap that protects your legacy and fuels your ambition.
Architecting Your 2026 Defense Strategy
Navigating the 2026 threat landscape requires a shift from fragmented tool sprawl toward a unified, bespoke architecture. Organizations must prioritize the integration of specialized MDR and DLP capabilities to maintain operational resilience. Aligning your digital infrastructure with the UAE Information Assurance (ISR) standards and the Personal Data Protection Law (PDPL) isn’t just a compliance task; it’s a strategic move to safeguard your growth within the Emirates. Industry data suggests that a proactive posture can reduce breach-related costs by up to 40% compared to reactive measures.
OAD Technologies provides Dubai-based expertise that meets global engineering standards. We don’t offer generic fixes. Our team focuses on building enterprise cybersecurity solutions tailored to your specific operational needs and GRC requirements. By bridging the gap between high-level innovation and practical results, we ensure your security stack is both scalable and robust. It’s time to move past temporary patches and invest in a future-proof system that protects your digital relevance for the next decade.
Consult with our Expert Architects to secure your enterprise
Your path to a more resilient and compliant enterprise is ready for construction.
Frequently Asked Questions
What are the essential components of enterprise cybersecurity solutions in 2026?
Enterprise cybersecurity solutions in 2026 rely on AI-driven behavioral analytics and quantum-resistant encryption to stay ahead of sophisticated threats. These tools allow organizations to identify anomalies 40% faster than traditional signature-based methods. OAD Technologies builds these frameworks to include identity-first security and automated incident response. By 2026, 75% of UAE enterprises will prioritize sovereign cloud architectures to maintain local data control while scaling their digital infrastructure securely.
How does the UAE Personal Data Protection Law (PDPL) affect enterprise security?
The UAE Personal Data Protection Law, or Federal Decree Law No. 45 of 2021, mandates rigorous controls over how businesses process and store personal information. Organizations must appoint a Data Protection Officer and implement technical measures that prevent unauthorized access. Non-compliance carries significant risks, including administrative fines that can reach AED 1 million. We help clients re-architect their data flows to ensure every touchpoint meets these specific legal requirements.
What is the difference between MSSP and MDR services?
Managed Security Service Providers (MSSP) primarily focus on perimeter monitoring and log management, while Managed Detection and Response (MDR) emphasizes proactive threat hunting. MSSPs keep the lights on by managing firewalls; MDR uses advanced telemetry to find attackers already inside the network. Statistics show that MDR services can reduce the average dwell time of a breach from 200 days to less than 24 hours, providing a more aggressive defense posture.
Can OAD Technologies help with NESA and ISR compliance in Dubai?
OAD Technologies provides specialized consultancy to ensure your infrastructure aligns with NESA and ISR standards in Dubai. We design bespoke roadmaps that map your current security controls against the 188 mandatory requirements set by the Dubai Electronic Security Center. Our team has guided over 50 local entities through the audit process, ensuring they achieve 100% compliance while maintaining operational efficiency and avoiding the penalties associated with regulatory gaps.
How often should an enterprise conduct VAPT assessments?
Enterprises should conduct Vulnerability Assessment and Penetration Testing (VAPT) at least twice a year or whenever they implement a major system update. Since 60% of new vulnerabilities appear within 30 days of a software patch, annual testing isn’t enough to secure modern environments. Regular VAPT provides a real-time view of your risk profile; this allows you to patch critical flaws before malicious actors exploit them during targeted regional campaigns.
What is the ROI of implementing a Data Loss Prevention (DLP) solution?
Implementing a Data Loss Prevention (DLP) solution yields an average ROI of 312% over three years by preventing intellectual property theft and regulatory fines. In the UAE, the average cost of a single data breach has risen to AED 25 million, making the initial investment in DLP highly cost-effective. These enterprise cybersecurity solutions protect your most valuable assets, ensuring that sensitive data doesn’t leave the corporate perimeter through unauthorized channels or accidental employee errors.
Is Zero Trust Architecture applicable to legacy on-premise systems?
Zero Trust Architecture is fully applicable to legacy on-premise systems through the use of identity-aware proxies and micro-segmentation. You don’t need to replace your entire infrastructure to adopt this model. Since legacy systems often represent 45% of an enterprise’s attack surface in the UAE, wrapping them in a Zero Trust framework is essential. We implement granular access controls that verify every user and device, even if the application is decades old.


