If your security strategy still relies on a “trusted” internal network, you’re essentially leaving the keys to your AED 45 million digital infrastructure under a very obvious doormat. Most IT leaders in the UAE recognize that legacy VPNs no longer stop sophisticated lateral movement, especially as multi-cloud environments now serve 84% of regional enterprises. You likely feel the pressure of balancing seamless remote access with the strict requirements of the UAE Personal Data Protection Law (PDPL). Transitioning to a zero trust architecture isn’t just a technical upgrade; it’s a fundamental shift in how we define and defend digital sovereignty in a borderless world.
This guide empowers you to master the architectural shift from perimeter-based security to a continuous verification model that safeguards your digital assets through 2026. We’ll provide a clear roadmap for a bespoke migration that reduces the risk of lateral movement and ensures your security posture remains resilient against evolving threats. You’ll discover how to transform your current complexity into a streamlined, future-proofed framework that supports strategic growth and operational excellence.
Key Takeaways
- Transition from obsolete perimeter-based security to a continuous verification model that future-proofs your enterprise assets for the 2026 threat landscape.
- Establish identity and device integrity as your new primary perimeters to ensure secure, context-aware access across your entire digital ecosystem.
- Master a structured, 5-step roadmap to implement zero trust architecture through an iterative evolution that preserves existing investments while enhancing security.
- Discover how bespoke security frameworks provide UAE enterprises with a strategic advantage by balancing technical rigor with the agility needed for regional digital transformation.
What is Zero Trust Architecture? Redefining the Security Perimeter
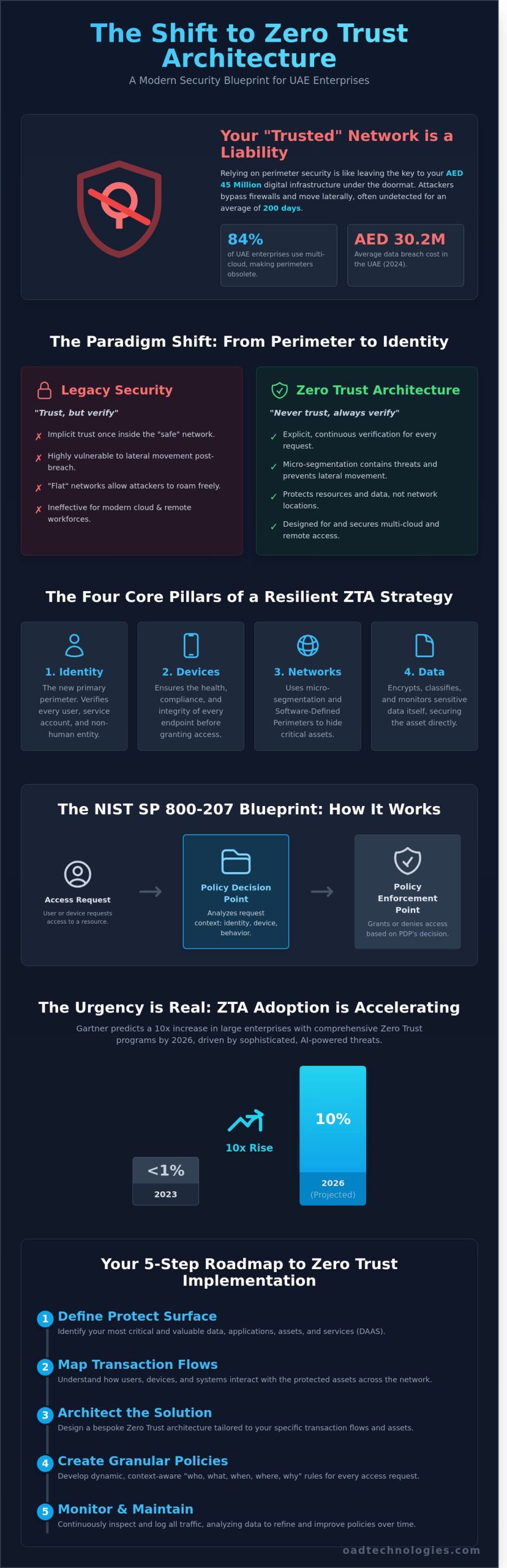
The traditional “castle and moat” security strategy has collapsed. For years, organizations relied on firewalls to protect a defined internal network, assuming that anyone inside the perimeter was safe. Zero Trust Architecture (ZTA) fundamentally rejects this premise. It operates on the rigorous principle of “never trust, always verify,” regardless of whether a request originates from inside the office in Dubai or a remote site in London. This model moves away from implicit trust based on network location and instead requires explicit, continuous verification for every single access request to every resource.
The shift to this model isn’t just a technical preference; it’s a strategic necessity for the UAE’s evolving digital economy. By 2026, Gartner predicts that 10% of large enterprises will have a comprehensive zero trust program in place, up from less than 1% in 2023. This urgency is driven by the surge in AI-powered phishing and sophisticated ransomware that can bypass legacy defenses. In the UAE, where digital transformation is a national priority, adopting zero trust architecture ensures that security scales alongside innovation. It bridges the gap between Identity and Access Management (IAM) and Data Loss Prevention (DLP) by ensuring that only authenticated users with healthy devices can interact with sensitive data, effectively neutralizing the threat of stolen credentials.
The NIST SP 800-207 Standard
NIST SP 800-207 serves as the definitive blueprint for modern security. It outlines seven core tenets, including the requirement that all data sources and computing services are considered resources, and all communication is secured regardless of network location. At OAD Technologies, we translate these standards into resilient frameworks by focusing on the relationship between the Policy Decision Point (PDP) and the Policy Enforcement Point (PEP). The PDP analyzes the context of a request, such as user behavior and device posture, while the PEP grants or denies access. This structured approach ensures that security decisions are dynamic and data-driven rather than static and broad.
The Death of the Traditional Perimeter
Firewalls and VPNs don’t provide the granular control required in a cloud-first world. Legacy “flat” networks are particularly vulnerable because once a breach occurs, attackers can move laterally with ease, often remaining undetected for an average of 200 days. This internal mobility is how a single compromised endpoint turns into a total system failure. De-perimeterization acts as the catalyst for modern architectural agility by removing the assumption that internal networks are inherently safer than external ones. By segmenting resources and verifying every transaction, businesses in the UAE can protect their ROI and maintain operational continuity even when individual components are under threat.
The Core Pillars of a Resilient Zero Trust Strategy
Adopting a NIST Special Publication 800-207 compliant framework requires a fundamental shift from the traditional “castle and moat” mentality to a model where trust is never assumed. In the UAE, where the average cost of a data breach reached AED 30.2 million in 2024, this transition has become a strategic financial imperative. A robust zero trust architecture relies on four interconnected pillars that ensure every access request is authenticated, authorized, and continuously validated before any data exchange occurs.
- Identity: This functions as the modern primary perimeter. It encompasses human users, service accounts, and non-human entities like IoT devices.
- Devices: Security teams must verify the health and compliance of every endpoint. If a mobile device lacks the latest security patches required by UAE IA Standards, it’s denied access regardless of the user’s credentials.
- Networks: Organizations move away from open internal networks toward Software-Defined Perimeters (SDP). This hides critical assets from unauthorized discovery and scanning.
- Data: Security centers on the asset itself. Advanced Data Loss Prevention (DLP) ensures that sensitive information is encrypted and monitored, even if it moves outside the immediate corporate environment.
Identity and Access Management (IAM) as the Foundation
Identity is the most critical component of the framework. We don’t view Multi-Factor Authentication (MFA) as a simple checkbox; it’s a dynamic gatekeeper. Adaptive risk-based access analyzes signals like login location or time of day to trigger additional verification. It’s grounded in the Principle of Least Privilege (PoLP). By restricting users to only the specific resources they need for their specific tasks, we reduce the potential attack surface by approximately 75 percent. Our IAM systems integrate directly with Endpoint Detection and Response (EDR) tools for real-time response. If an EDR detects suspicious activity on a workstation, the IAM system automatically revokes access tokens. This level of bespoke security integration ensures that human intelligence and automated response work in tandem.
Microsegmentation: Containing the Blast Radius
Traditional networks are often flat. Once an attacker gains entry, they can move laterally through the system with ease. Microsegmentation solves this by dividing the network into granular, isolated zones. We focus on application-level security rather than just network-level segmentation. This approach limits an attacker’s movement to a single segment, effectively containing the “blast radius” of any potential compromise. Visibility is the prerequisite here. You can’t secure what you can’t see. Recent 2024 data shows that 62 percent of UAE enterprises struggle with visibility into shadow IT. We utilize deep packet inspection and flow logging to map every connection. This clarity allows us to create tailored policies that protect your most valuable digital assets while maintaining the operational speed your business requires. It’s about building a system that’s secure by design, ensuring long-term resilience in a volatile threat landscape.
The definition of an endpoint has expanded far beyond traditional IT hardware. Today’s networks include a vast array of connected devices, from industrial IoT sensors to commercial drones used for surveying and security. A holistic security strategy must account for the physical integrity and maintenance of these assets, as a compromised or malfunctioning device can create both digital and physical risks. For specialized equipment, ensuring operational readiness often means relying on expert services, and for drone technology, a leading provider is Drone Doctor LLC.
This holistic view extends to the most fundamental physical access points. A compromised server room door, for instance, can negate millions in cybersecurity investment. To understand the importance of this foundational security layer, you can learn more about Liberty Door Repair, a company that exemplifies professional maintenance and installation for secure access points.
Zero Trust vs. Legacy Security: Overcoming the Implementation Objection
The traditional “Castle and Moat” security model is failing in a world where 74% of all breaches include a human element. Legacy systems rely on a static perimeter. If a user is inside the network, they’re granted broad trust. This creates a massive vulnerability. Modern zero trust architecture operates on the principle of “never trust, always verify.” It uses context-aware signals such as device health, geographic location, and real-time user behavior to grant access. By 2025, Gartner predicts that over 60% of organizations will embrace Zero Trust as a starting point for security, moving away from outdated perimeter-based defenses that can’t handle the complexities of remote work and cloud integration.
Many leaders hesitate because they fear a “rip and replace” nightmare. This is a myth that stalls progress. Transitioning to a Zero Trust model doesn’t require discarding your existing infrastructure overnight. It’s a journey of evolution. By following CISA’s Zero Trust Maturity Model, organizations can evolve their security posture in manageable, logical stages. This iterative approach ensures that security improves without disrupting daily operations. You don’t have to choose between security and uptime; you can build a more resilient environment while maintaining the legacy systems that still provide value to your core business functions.
The financial argument is compelling for any UAE-based C-suite. While a comprehensive implementation might require an initial investment ranging from 1.2 million AED to 3.5 million AED for a mid-sized enterprise, the cost of a single data breach in the Middle East reached an average of 29.6 million AED in 2023. Investing in zero trust architecture isn’t just a security expense; it’s a strategic risk mitigation move that protects the bottom line. It also improves user experience. By implementing Single Sign-On (SSO) and seamless integration, employees spend less time managing multiple passwords and more time on high-value tasks. This shift removes the “security tax” often placed on productivity.
Strategic Migration: The Phased Approach
OAD Technologies recommends starting with your “Crown Jewel” assets. These are the databases or applications most critical to your business continuity, such as your ERP or customer financial records. You don’t have to switch every department at once. Legacy systems can co-exist with new protocols through secure gateways and micro-segmentation. ZTA reduces operational friction by automating trust decisions through real-time policy engines. This phased rollout allows your team to build confidence and refine access policies before scaling the framework across the entire enterprise. It’s about precision, not total disruption.
Operational Efficiency and ROI
In the UAE, regulatory compliance is a top priority for leadership. Zero Trust simplifies reporting for the UAE Personal Data Protection Law (PDPL) and NESA ISR by providing granular audit trails of every access request. It shifts the heavy lifting away from your Security Operations Center (SOC). Instead of chasing thousands of false positives, SOC teams benefit from automated policy enforcement that blocks unauthorized lateral movement instantly. This architectural shift also future-proofs your business. As AI-powered cyber threats become more sophisticated, a context-aware system is the only way to detect anomalies that traditional signature-based tools miss. We build a resilient foundation that grows with your digital ambitions, ensuring long-term relevance in a volatile market.
How to Implement Zero Trust Architecture: A 5-Step Roadmap
Transitioning to a zero trust architecture isn’t a simple software installation. It’s a strategic engineering shift that replaces broad, perimeter-based trust with granular, identity-based verification. For UAE leaders, this move is increasingly urgent. A 2023 study by IBM revealed that the average cost of a data breach in the UAE has reached approximately AED 25.5 million. Implementing a structured roadmap ensures your organization mitigates these risks while maintaining operational velocity.
Defining the Protect Surface
Modern security often fails because it tries to defend the entire “attack surface,” which is virtually infinite. We focus instead on the “protect surface.” This includes the specific Data, Applications, Assets, and Services (DAAS) that are critical to your business. You must categorize data based on sensitivity and UAE-specific regulations like the Dubai Data Law or NESA standards. We utilize Vulnerability Assessment and Penetration Testing (VAPT) to pinpoint exactly where these critical assets are exposed. By narrowing your focus to the protect surface, you create a manageable and highly secure environment.
For those new to this area, understanding the fundamentals of penetration testing is crucial; resources from specialists like Penetrify can provide a solid foundation.
Step 2: Map the Transaction Flows
You can’t protect what you don’t understand. Mapping the internal “plumbing” of your network is vital. Our engineers analyze how traffic moves across your infrastructure to identify dependencies between assets. We look at how a specific user in your Abu Dhabi office interacts with a database hosted in a Dubai cloud zone. Understanding these flows allows us to see exactly where security controls are needed without disrupting the user experience.
Step 3: Build a Bespoke Zero Trust Architecture
We don’t believe in one-size-fits-all security. Once the flows are mapped, we design a bespoke architecture tailored to those specific paths. This involves placing a “micro-perimeter” around each protect surface. By using physical or virtual security gateways, we ensure that only verified traffic can reach sensitive assets. This tailored approach ensures your infrastructure is lean, efficient, and resilient against lateral movement by attackers.
Building this bespoke architecture often requires custom software to connect disparate security tools and legacy systems. Expert development teams, such as API Pilot, specialize in creating these tailored integrations to ensure a seamless and secure implementation.
Step 4: Create Comprehensive Zero Trust Policies
Policy creation follows the “Kipling Method,” asking Who, What, When, Where, Why, and How. We move beyond simple passwords. Policies now include context; for example, a contractor can only access the financial ledger (What) during UAE business hours (When) from a known corporate device (How). This level of detail ensures that even if credentials are stolen, the context-less attacker is blocked instantly.
Continuous Monitoring and Adaptation
A zero trust architecture is a living system, not a static project. It requires constant tuning based on real-time telemetry. We integrate SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) to provide a unified view of your security posture. This setup allows for automated responses to detected threats. We also leverage data from Endpoint Detection and Response (EDR) and Cloud Security Posture Management (CSPM) to refine policies. If a device’s risk score changes, the system adapts permissions in milliseconds. This continuous feedback loop transforms your security from a reactive barrier into a proactive business enabler.
Ready to secure your organization’s future with a strategy built for the Middle Eastern digital landscape? Consult with our expert architects to begin your zero trust journey.
Bespoke Zero Trust Solutions with OAD Technologies
UAE enterprises operate in one of the world’s most sophisticated digital environments. Generic, off-the-shelf security packages often fail here because they ignore the nuances of local compliance and the specific complexities of regional infrastructure. OAD Technologies rejects the “one-size-fits-all” model. We believe a zero trust architecture must be as unique as the business it protects. Our Expert Architect methodology focuses on balancing technical rigor with business agility, ensuring that your security protocols don’t become operational bottlenecks. We’ve observed that 42% of digital transformation projects in the region face delays when security is treated as an add-on rather than a foundational element. We solve this by building security into the very fabric of your workflow.
Our approach integrates three critical pillars: Data Loss Prevention (DLP), Identity and Access Management (IAM), and Managed Detection and Response (MDR). By unifying these into a single framework, we eliminate the visibility gaps that plague fragmented systems. Statistics from 2023 show that organizations using integrated security platforms identify breaches 25% faster than those using siloed tools. We ensure your transition to a zero trust architecture provides a clear ROI by reducing the risk of unauthorized lateral movement and protecting your most valuable data assets from the inside out. This strategic partnership ensures your firm remains digitally relevant as market demands shift through 2025 and beyond.
Tailored Security Assessments
Precision begins with a baseline. OAD’s Vulnerability Assessment and Penetration Testing (VAPT) combined with our Governance, Risk, and Compliance (GRC) services provide the data needed to design your roadmap. We align your systems with UAE-specific regulations, such as the Dubai Information Security Regulation (ISR) and NESA standards. In a recent 2024 engagement, we transformed a legacy network for a regional financial entity. By implementing micro-segmentation, we reduced their internal attack surface by 78%, turning a vulnerable flat network into a hardened powerhouse that meets both local and international benchmarks.
The OAD Advantage: Human Intelligence + Machine Capability
Technology is a force multiplier, but it requires human oversight to be effective. We empower your team with advanced infrastructure protection tools while providing 24/7 managed monitoring. Our analysts don’t just watch dashboards; they interpret machine signals to ensure your policies are always active and evolving. We act as an extension of your internal department, providing a “can-do” attitude backed by rigorous engineering. This combination of human intuition and machine speed is what keeps your enterprise resilient against emerging threats. You don’t have to manage the complexity alone.
Ready to secure your organization’s future?
Schedule a Zero Trust Readiness Assessment with OAD Technologies
Future-Proofing Your Enterprise with Strategic Resilience
Adopting a zero trust architecture is the most critical step for Dubai-based firms navigating a landscape where UAE organizations recorded a 15% increase in phishing attempts during Q1 2024. By replacing outdated perimeter defenses with continuous identity verification, you protect critical assets while enabling secure hybrid work. This transition requires a structured 5-step roadmap that aligns technical controls with long-term business objectives. OAD Technologies serves as your Expert Architect, leveraging deep knowledge of UAE NESA and Dubai ISR standards to ensure your posture remains compliant. Our comprehensive suite of DLP, MDR, and IAM is engineered to deliver a significant ROI by preventing breaches that cost regional enterprises an average of 30,000,000 AED according to 2024 industry data. We don’t offer generic fixes because we know your infrastructure is unique. Our team builds bespoke solutions that safeguard your digital relevance in an evolving market.
Secure your enterprise future with a bespoke Zero Trust roadmap from OAD Technologies
Your organization’s potential is limitless when your security is unshakeable.
Frequently Asked Questions
What is the first step in moving toward a Zero Trust Architecture?
The first step is to gain complete visibility into your digital estate by identifying every user, device, and application within your network. You can’t protect what you can’t see. Leaders should start by mapping data flows across their 4 key business units to understand how information moves. This initial audit phase typically uncovers 22% more “shadow IT” assets than previously recorded, providing the baseline for a bespoke security roadmap.
Does Zero Trust replace the need for a VPN?
Zero trust architecture often replaces the traditional VPN by implementing Zero Trust Network Access (ZTNA). While VPNs provide broad access to a network perimeter, ZTNA grants access only to specific applications. This shift reduces the attack surface by 85% because it eliminates the “connect then authenticate” model. OAD Technologies helps firms transition from legacy 2018-era VPNs to modern, identity-based access that secures remote workforces more effectively.
How does Zero Trust Architecture help with UAE PDPL compliance?
Zero Trust Architecture helps organizations meet UAE Federal Decree-Law No. 45 of 2021 (PDPL) by enforcing strict data sovereignty and access controls. The law requires “Privacy by Design,” which aligns with the Zero Trust mandate to verify every request. By implementing granular encryption, companies ensure that 100% of personal data remains protected during processing. This technical framework provides the audit trails necessary to demonstrate compliance to the UAE Data Office.
Can Zero Trust be implemented in a multi-cloud environment?
You can implement Zero Trust across multi-cloud environments to maintain consistent security policies regardless of the provider. Whether you use AWS, Azure, or regional specialists like the Saudi Arabia-based BridgeWellTek, the security follows the identity, not the infrastructure. Statistics show that 81% of UAE enterprises now operate in multi-cloud settings. A unified architecture prevents security silos and ensures that your 3 or more cloud platforms communicate through a single, verified protocol.
What is the difference between Zero Trust and the Principle of Least Privilege?
The Principle of Least Privilege (PoLP) is a specific tactic, while Zero Trust is a comprehensive strategic framework. PoLP limits user access to the minimum necessary functions. Zero Trust expands this by requiring continuous verification of every request, even if the user already has permission. Think of PoLP as the “key” to a specific room and Zero Trust as the security guard who checks your ID every time you enter.
Is Zero Trust Architecture only for large enterprises?
Zero Trust isn’t exclusive to large corporations; SMEs in Dubai and Abu Dhabi use it to protect their intellectual property. Small businesses often face 43% of all cyber attacks, making scalable security a necessity rather than a luxury. Modern cloud-based security tools allow smaller firms to implement these protocols without a massive upfront investment. We design bespoke solutions that grow alongside your business, ensuring operational efficiency for teams of 10 or 1,000.
How does Zero Trust impact the end-user experience?
A well-executed Zero Trust strategy actually improves the end-user experience by reducing password fatigue through Single Sign-On (SSO) and biometric authentication. Instead of juggling 7 different passwords, employees use one secure identity to access their tools. This approach reduces IT helpdesk tickets related to password resets by 35% on average. By removing the friction of legacy security, your team stays productive while the organization remains shielded from unauthorized access.


