
Zero Trust Architecture (ZTA) has become one of the most essential cybersecurity frameworks for modern businesses in 2025. As companies expand digitally, operate remote teams, and manage sensitive customer data, traditional perimeter-based security no longer provides adequate protection.
Zero Trust offers a modern, intelligent, and highly adaptive approach — and is now widely adopted by BPOs, CX centers, IT service companies, banks, government entities, and global enterprises.
In this guide, OAD Technologies breaks down Zero Trust in simple, business-friendly language to help you understand what it is, why it matters, and how your organization can implement it effectively.
What Is Zero Trust Architecture? (Simple Explanation)
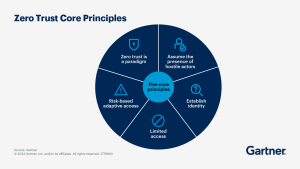
Zero Trust is a cybersecurity model built on a strict principle:
“Never trust. Always verify.”
Instead of assuming that users or devices inside your network are safe, Zero Trust continuously validates:
- User identity
- Device integrity
- Access behaviour
- Network activity
- Permissions & privileges
This approach dramatically reduces the risk of:
- Data breaches
- Insider threats
- Credential theft
- Malware spread
- Unauthorized access
- Lateral movement
This is why top global customer service companies and international call centers rely heavily on Zero Trust to safeguard customer data.
Why Zero Trust Is Critical for Businesses in 2025
1. Remote & Hybrid Work Environments
Employees today access company resources from:
- Home networks
- Public WiFi
- Mobile devices
- Cloud platforms
Zero Trust ensures secure access anywhere, anytime.
2. Rise in Advanced Cyber Threats
Attackers now use:
- AI-powered phishing
- Social engineering
- Deepfake voice fraud
- Password hacking
- Compromised devices
Zero Trust adds multiple layers of verification — blocking attacks before they escalate.
3. Client & Compliance Requirements
Enterprise clients increasingly require Zero Trust in their contracts and audits.
Implementing ZTA helps you achieve:
- ISO 27001
- GDPR
- HIPAA
- PCI DSS
- UAE personal data protection compliance
It also enhances trust and improves your competitive edge.
How Zero Trust Works: Simple Breakdown
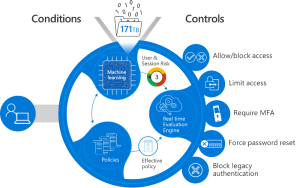
1. Verify Every User (Identity Protection)
No user is trusted automatically.
Verification methods include:
- Multi-factor authentication (MFA)
- Strong password policies
- Single Sign-On (SSO)
- Adaptive identity checks
This prevents unauthorized or fraudulent logins.
2. Verify Every Device (Endpoint Security)
Before a device accesses your systems, Zero Trust checks:
- OS and patch status
- Antivirus health
- Device identity
- Risk score
- Geolocation
Only secure devices are allowed into your network.
3. Least Privilege Access
Users get only the access they need.
Example:
- Agents → Only agent tools
- HR → HR systems only
- Finance → Financial data only
This reduces internal risks and limits breach impact.
4. Continuous Monitoring & Analytics
Zero Trust constantly analyzes:
- Login patterns
- Data movement
- Unusual access attempts
- Internal activity
If behavior looks suspicious, access is restricted instantly.
5. Micro-Segmentation
Your network is divided into smaller zones.
So if an attacker enters one segment…
they cannot move further.
This keeps breaches fully contained.
Key Benefits of Zero Trust for Businesses
 Protects customer interactions & call logs
Protects customer interactions & call logs
 Stronger defense against cyberattacks
Stronger defense against cyberattacks
 Supports global compliance requirements
Supports global compliance requirements
 Reduces internal & accidental misuse
Reduces internal & accidental misuse
 Enhances client trust & reputation
Enhances client trust & reputation
 Improves operational security efficiency
Improves operational security efficiency
 Protects cloud, on-prem, and hybrid environments
Protects cloud, on-prem, and hybrid environments
Companies with Zero Trust experience significantly fewer breaches and recover faster when incidents occur.
How Your Business Can Get Started With Zero Trust
OAD recommends beginning with these essential steps:
1. Identify users, roles & access levels
Map who needs access to what.
2. Implement MFA across all applications
This instantly increases security.
3. Enforce device validation
Allow only compliant, secure devices.
4. Apply least privilege access
Reduce unnecessary access rights.
5. Set up continuous monitoring
Track abnormal behaviour in real time.
6. Review access policies regularly
Update as teams and processes evolve.
Zero Trust Services by OAD Technologies
OAD Technologies provides end-to-end Zero Trust implementation tailored for businesses in the UAE, GCC, India, and global markets.
Our services include:
 Zero Trust Roadmap Development
Zero Trust Roadmap Development Identity & Access Management (IAM)
Identity & Access Management (IAM) Device & Endpoint Verification
Device & Endpoint Verification Network Micro-Segmentation
Network Micro-Segmentation Multi-layer Threat Monitoring
Multi-layer Threat Monitoring AI-powered Anomaly Detection
AI-powered Anomaly Detection Compliance Mapping (ISO, GDPR, UAE)
Compliance Mapping (ISO, GDPR, UAE) Cybersecurity Awareness Training
Cybersecurity Awareness Training
We help you secure operations without affecting workflow or productivity.
Schedule Your Free Zero Trust Security Assessment
 Call / WhatsApp: +971 4 372 4997
Call / WhatsApp: +971 4 372 4997
 Email: info@oadtechnologies.
Email: info@oadtechnologies.
 Website: https://www.
Website: https://www.
Future-Proof Your Security With OAD Technologies
Zero Trust is not just a cybersecurity trend —
it is a must-have framework for any business that manages customer data or cloud-based operations.
With OAD Technologies by your side, you can:
 Safeguard sensitive data
Safeguard sensitive data
 Strengthen your compliance posture
Strengthen your compliance posture
 Win trust from enterprise clients
Win trust from enterprise clients
 Reduce breach risks
Reduce breach risks
 Modernize your security architecture
Modernize your security architecture
Ready to make your business safer, smarter, and fully Zero Trust–ready?
Let’s begin your transformation today.


